How to Unblock a Website: 7 Effortless Solutions for Any Situation
Bumped into a frustrating error message “The site can’t be reached” in your browser? Whether at home, at school, in the office, or during your vacation, being unable to access your favorite websites can be a real bummer. Luckily, there are several simple and practical solutions to this challenge, from a virtual private network (VPN) and proxy server to browser extensions and URL shorteners. Read along to find out how to unblock a website wherever you are and pick the best method for your needs. Let’s get started!

How to unblock websites with a VPN: Your quick guide
Are you in a hurry? Then check out a quick guide on how to bypass blocked sites with the help of a VPN. Take these simple steps to get the job done:
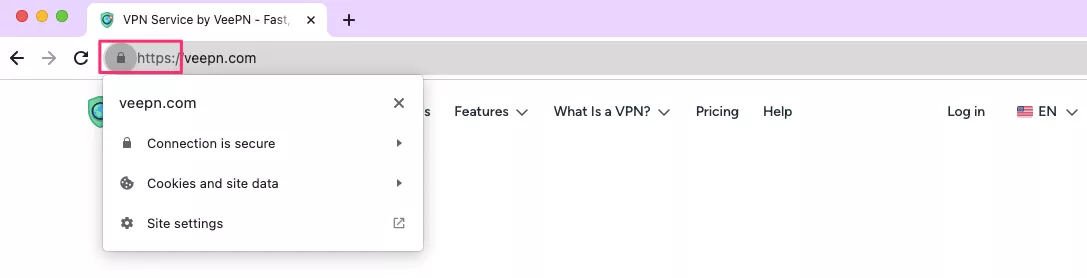
- Pick a credible VPN service provider. Consider VeePN – one of the best website unblockers out there.
- Choose your VeePN pricing plan and subscribe.
- Download and install the VeePN app on your device, be it a laptop, smartphone, tablet, smart TV, or gaming console.
- Connect to the most suitable server location – choose from 89 options available.
- Turn VeePN on.
- You’re all set! Open the websites of your choice without access limitations wherever you are.
And now, if you’re looking for details, let’s dive in and explore the most effective ways to unblock websites.
7 simple methods to unblock websites
Here’s the ultimate list of the best solutions that will allow you to get a website unblocked effortlessly.
1. Use a VPN
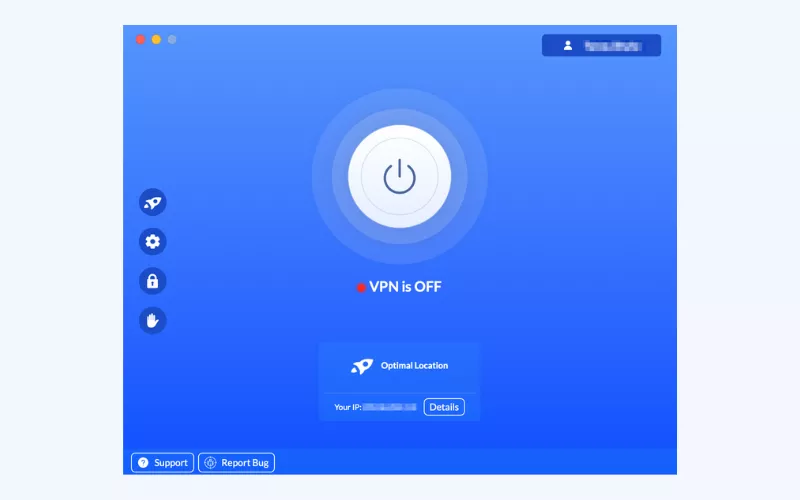
A virtual private network (VPN) is an advanced tool that hides your IP address and encrypts your Internet traffic. As a result, you can surf the web anonymously and access any website you need. This makes a VPN hands down the best method to unblock geo-restricted websites. Moreover, a premium VPN is not just an effective solution against various Internet limitations, including Wi-Fi and censorship restrictions. It also provides extra features to maintain your digital privacy and protect your sensitive information from hackers, snoopers, and other third parties.
So, what is the way a VPN unlocks websites? In a nutshell, it changes your actual IP with a new one that is linked to your preferred location. When turned on, the sites and services you are accessing will not be able to detect your true location and other information about your connection.
For example, you need to visit your favorite streaming service and watch a beloved show while on vacation in another country. But it turns out that the platform is unavailable in that location and doesn’t let you in. In this case, you can connect to a VPN server located in your home country, be it the US, the UK, Canada, or else. As a result, the service will only detect the anonymous IP provided by the VPN instead of the real one, having no reason to keep you out.
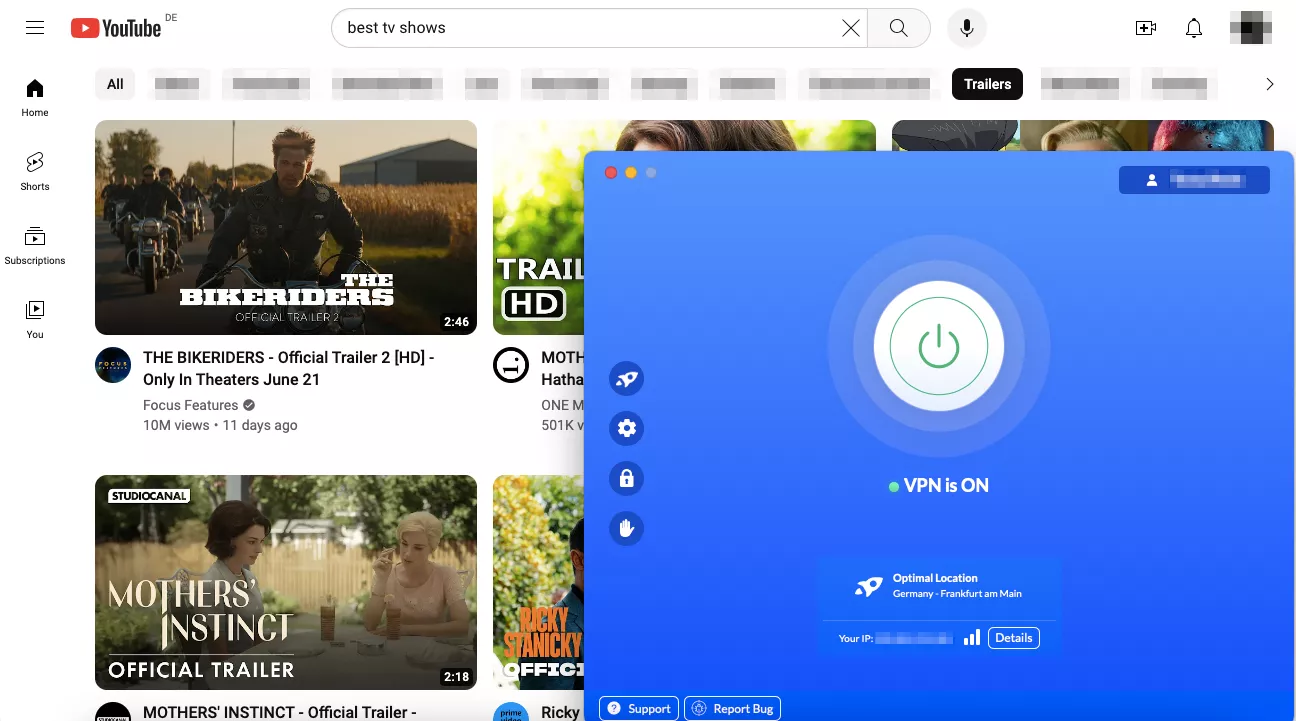
💡 Pro tip. Although not every VPN is effective and reliable. Using a free VPN could jeopardise your privacy since these services will collect data about customers and sell it to third parties. Use reliable and fully-fledged VPNs such as VeePN to unlock sites without damaging your Internet security. It will take you a little time to learn how to access your favorite sites with VeePN.
2. Use a proxy server
The other potential method of unblocking a website on the Internet is by accessing proxy services. Like a VPN, a proxy will also substitute your actual IP address and direct your traffic to a proxy server. In this manner, you will be able to use the Internet as though you were in a different location and break geo-blocks and other Internet restrictions.
However, proxies are comparatively good and convenient, but not as safe as VPNs. The issue is that a proxy does not encrypt your traffic, so third parties can follow your online trail and spy on you. Remember also that free proxies are not always safe, because they are usually accompanied by malicious advertisements, pop-ups and dodgy links.
Another significant downside of proxies is that they are easier to detect and block. Unlike VPNs with large server networks, they offer a limited number of IPs you can use. Big streaming platforms and other popular services often blacklist those addresses to prevent users from getting around geographical limitations. In our related blog post, you can learn more about the difference between VPNs and proxies.
3. Use a VPN browser extension
VPNs come not only in the form of full-fledged applications but also as extensions you can set up in your web browser. So if you’re wondering how to unblock websites on Chrome browser or another browser, this solution might be your go-to.
You can set up a VPN extension on your browser without downloading any software, which makes it even easier to use than a desktop or mobile app. What’s more, reputable VPN services like VeePN offer free extensions that will allow you to unblock sites on Chrome, Firefox, and Edge. They work similarly to apps, changing your IP and providing some extra features for your online protection and privacy.
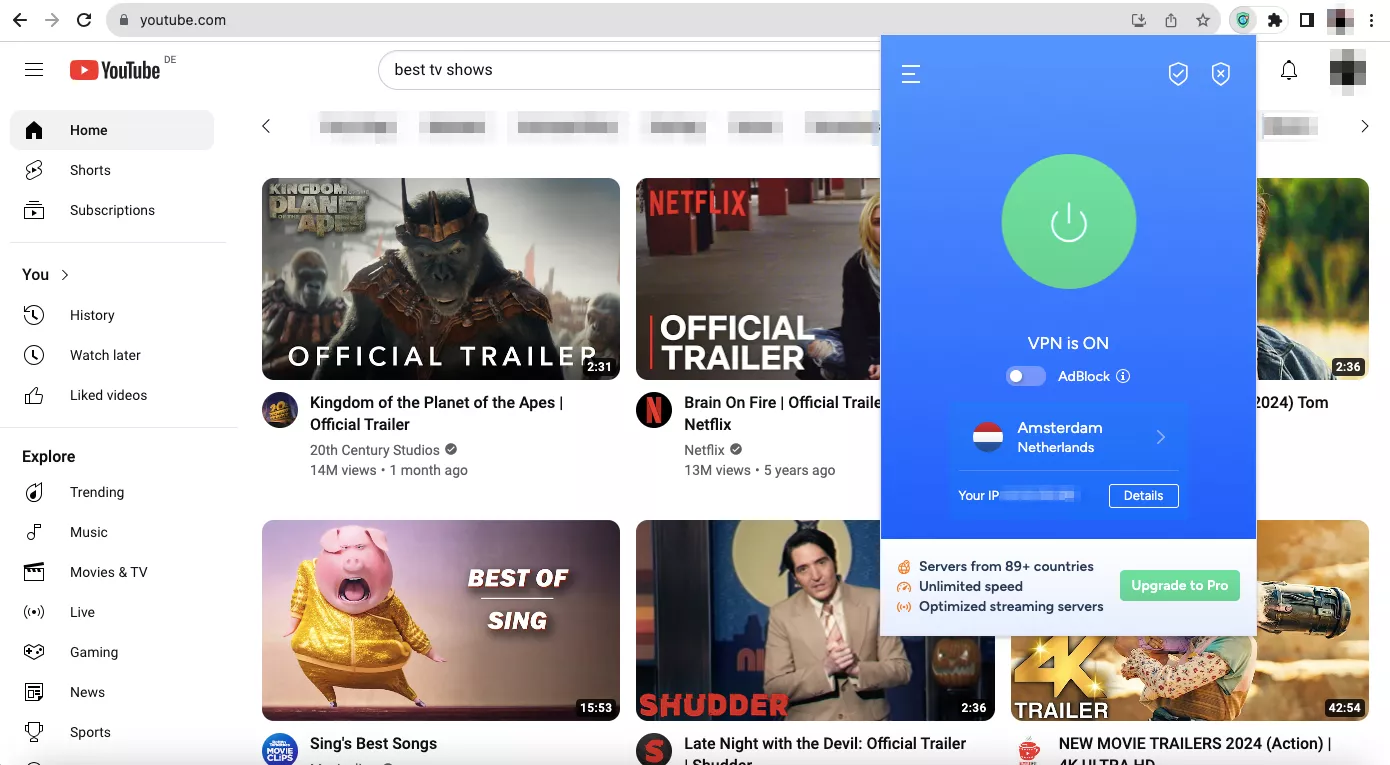
But it’s worth noting that a VPN extension is rather a lightweight version of the full application. While remaining one of the most popular and convenient website unblockers, its functionality is somewhat limited. Check out our recent blog post to find out more about the difference between a VPN app and an extension.
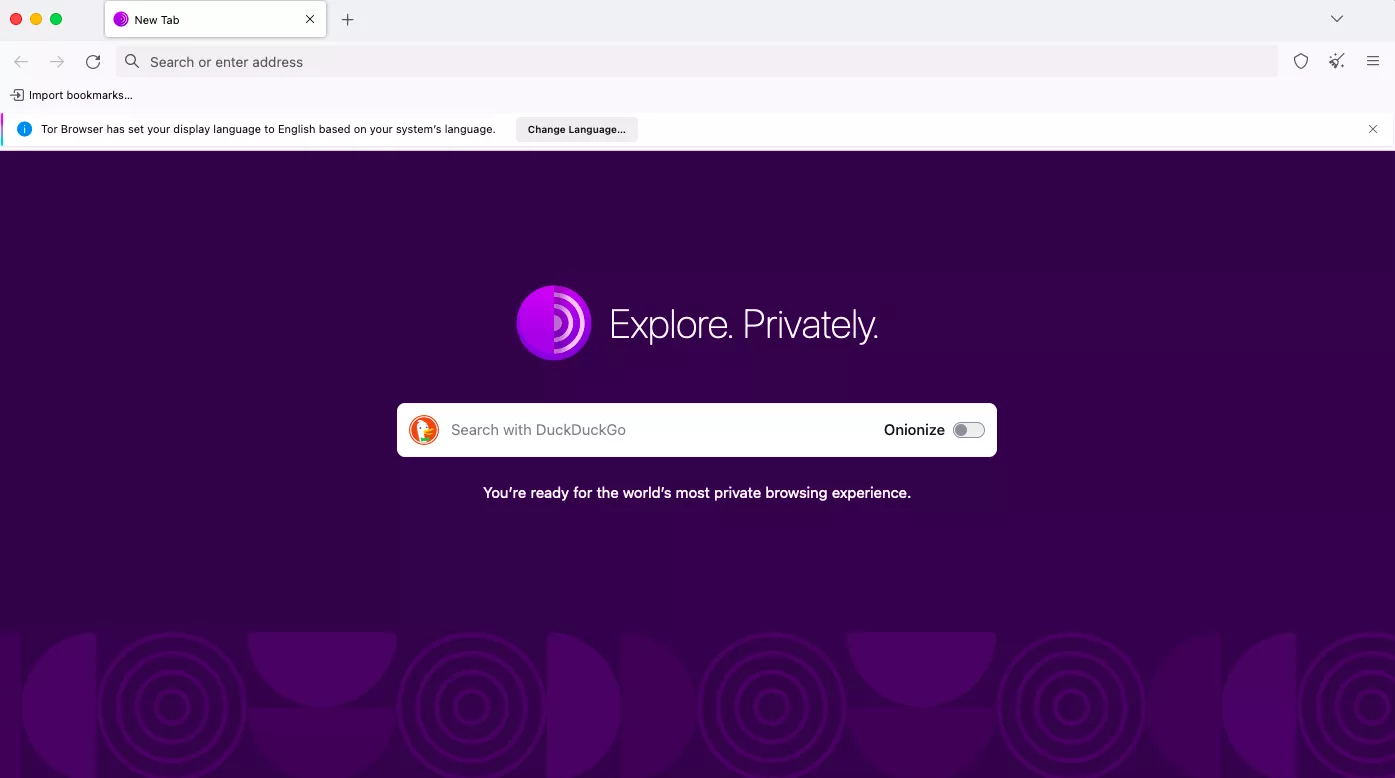
4. Use the Tor browser
The Onion Router (Tor) is a web browser designed for private online communication and anonymous access to the Internet. Apart from spoofing your IP address, Tor runs your traffic through several routers called nodes (the process is also known as onion routing). Also, Tor provides access to the dark web and helps overcome advanced Internet blocks. These features make Tor a popular solution for journalists, human rights activists, and even military agents.
But while Tor is a highly secure and powerful tool for anonymous access to the Internet, it’s not the best option to unblock websites. One of its main pitfalls is that Tor doesn’t allow you to pick the desired virtual location. Also, it significantly slows down your Internet speed, which is critical for a smooth streaming and gaming experience. Check out our blog post for a detailed comparison of VPN and Tor.
5. Turn URL into IP
If you’re not facing advanced blocks but rather local Wi-Fi restrictions, chances are your school or work administrators simply prevent access to specific URLs. It means that the IP address of this website or server is still accessible.
Now, what’s the difference between a URL and an IP address of a certain website? A URL is the actual address of the site (such as https://reddit.com). In turn, an IP address is a unique combination of numbers identifying the website on the Internet (for example, it could be 111.111.11.111). Typing these numbers into your browser’s address bar may take you to the blocked website if its IP isn’t blocked.
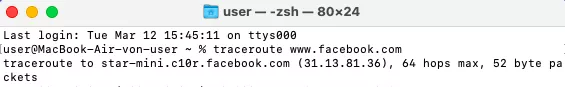
But here, you probably wonder how to find the IP address of a specific website. To do that, you use Command Prompt (Windows, Linux) or Terminal (Mac). Here’s what you should type to get the site’s IP:
- On Windows: Open Command Prompt > Enter ping and the website’s URL (like www.facebook.com) > Press Enter.
- On Linux: Open Command Prompt > Enter dig plus the URL > Press Enter.
- On Mac: Open Terminal > traceroute and the site’s URL > Press Enter.
6. Convert HTML into PDF
This solution will suit you if you only need to read the website’s content rather than access its fully functioning version. If that is your case, you can use a tool designed to convert web pages into common readable formats like PDF. Simply insert the site’s URL into the box using a free converter like Sejda, HTML2PDF, or Convertio. Once done, you’ll be able to access the page online or download it on your device.
But note that free converters will only provide access to pictures and text from a particular website. It won’t allow you to press any buttons, stream videos, send messages, and so on.
7. Access the cached version of the website
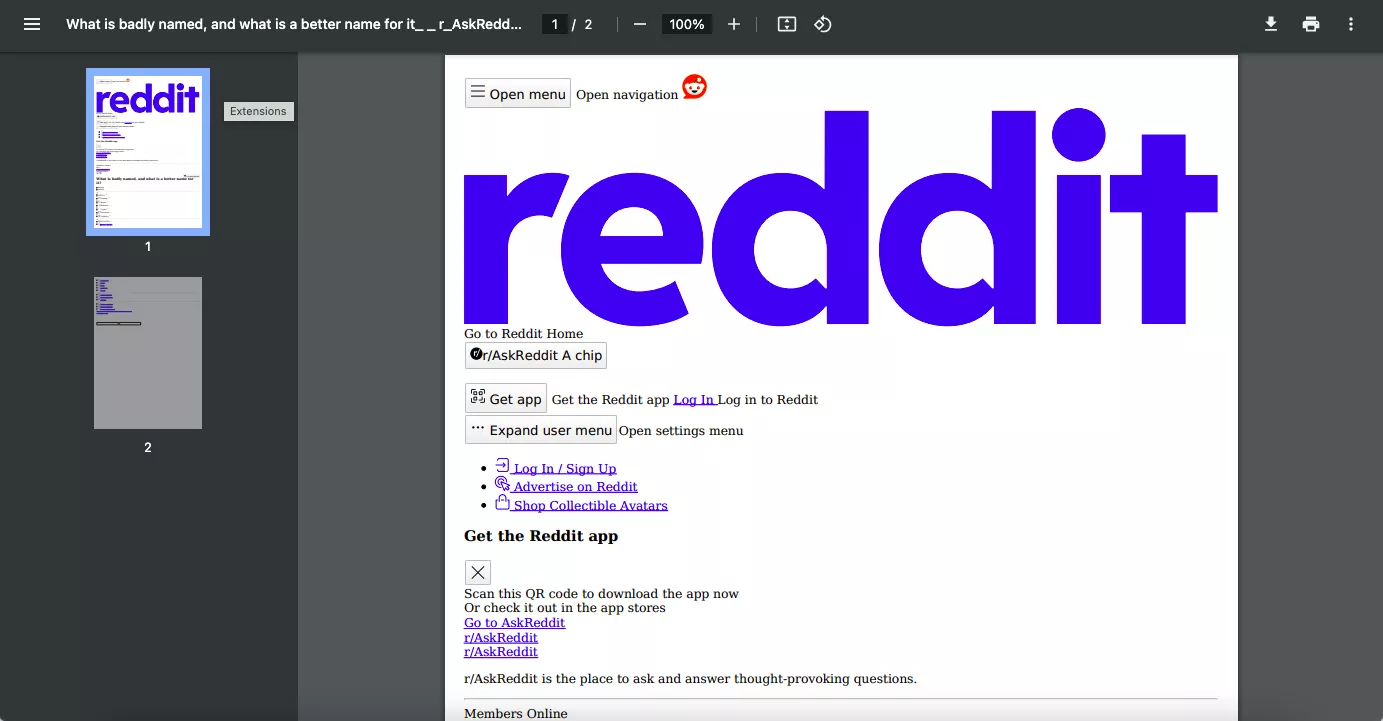
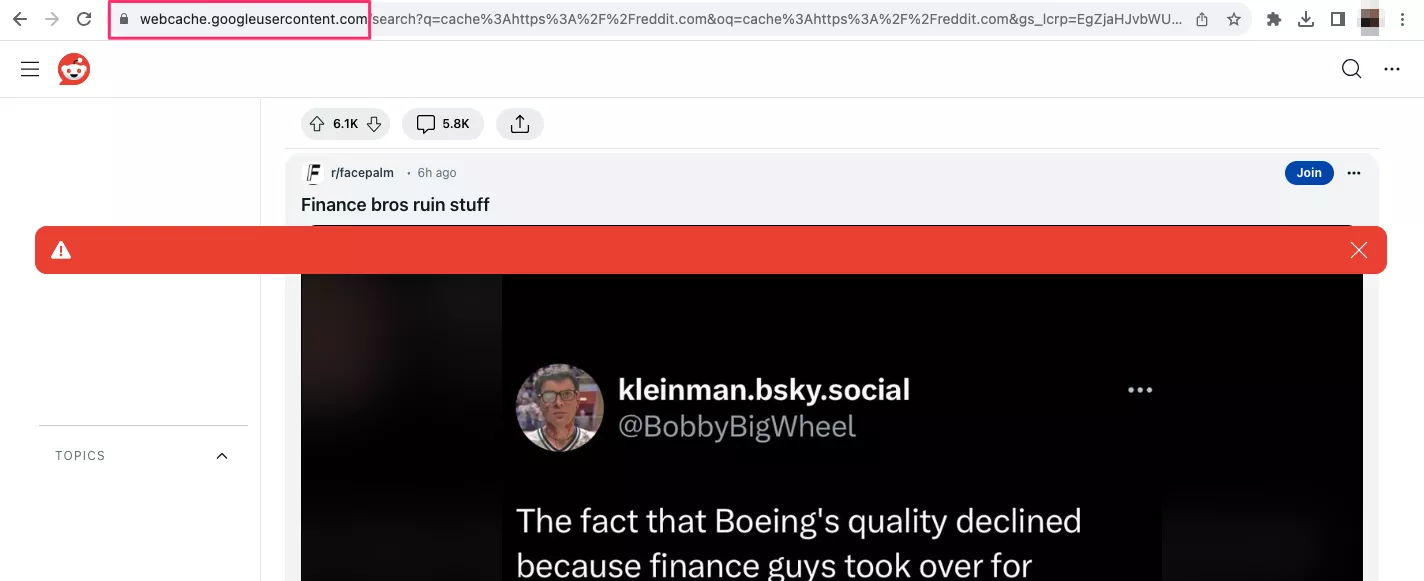
Every website indexed by Google has a cached version of its website data lying in the search engine’s temporary storage. And if a certain page is currently unavailable to you, it’s possible to open this version. To do that, follow these easy steps:
- Open a new window or tab in your browser.
- Type cache: before the URL of the website you want to access (for example, cache:https://www.reddit.com).
- Press Enter.
Remember, this method won’t always work – and even if it does, it won’t provide access to the actual page. Cached versions of websites often lack buttons, menu elements, images, and other important elements.
As you can see, there are lots of possible ways to unblock a website. On top of that, you can use several additional tricks, which are particularly useful if you’re not dealing with advanced blocking techniques like firewalls and deep packet inspection (DPI).
Extra tips on how to unblock websites
Here are some additional things you can do to check whether a website is really blocked and access it trouble-free.
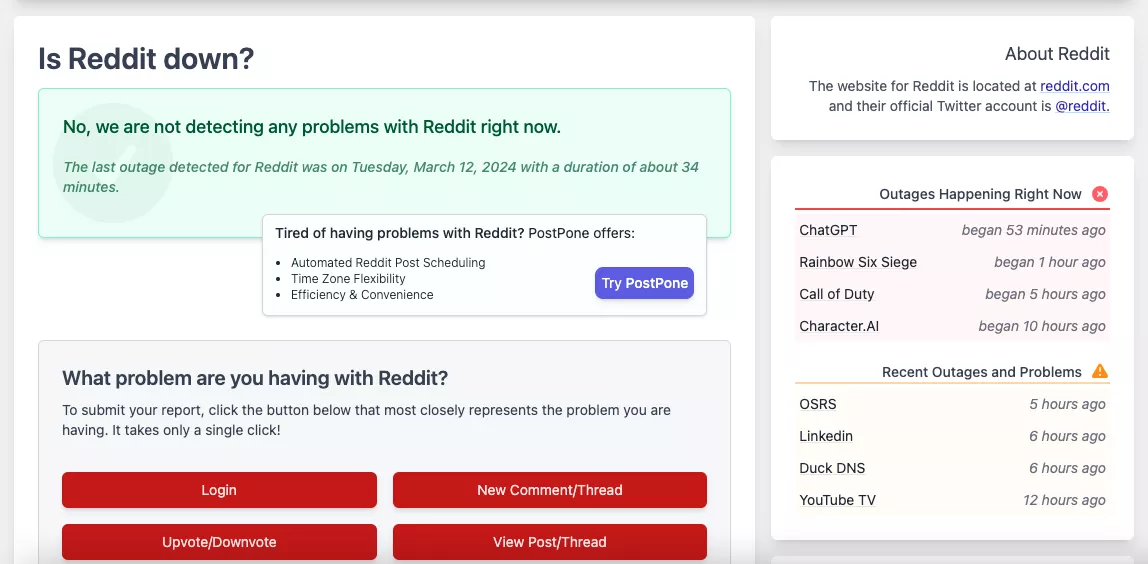
- Check whether the website is down just for you. It sometimes happens that a particular website is unavailable to all users due to technical issues, such as downtime, DDoS attacks, hosting problems, or DNS errors. So before turning to one of the unblocking techniques listed above, check why exactly the site doesn’t work. Use a free tool like isup.me, down.com, or isitdownorjust.me to find out what’s wrong. Not sure why you can access a specific website? Then you might learn whether your ISP is blocking you.
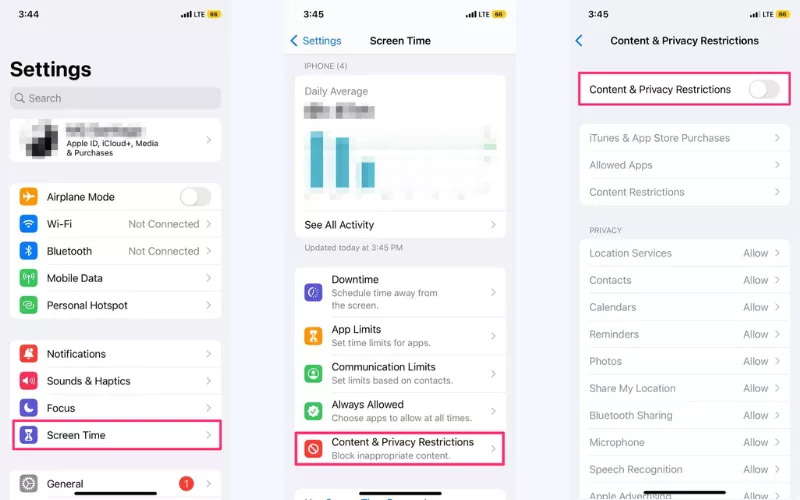
- Change your screen time limits. It may appear that the website isn’t actually blocked but can’t be opened because of screen time limits set on your mobile device. These are special restrictions mostly associated with parental control. But you may also forget about those limitations or even be unaware of them. Luckily, it’s easy to change your screen time limits. On an iOS device, open Settings > Screen Time > Content & Privacy Restrictions and toggle it off. On Android, you can find this setting in the Your Family section via your Google account.
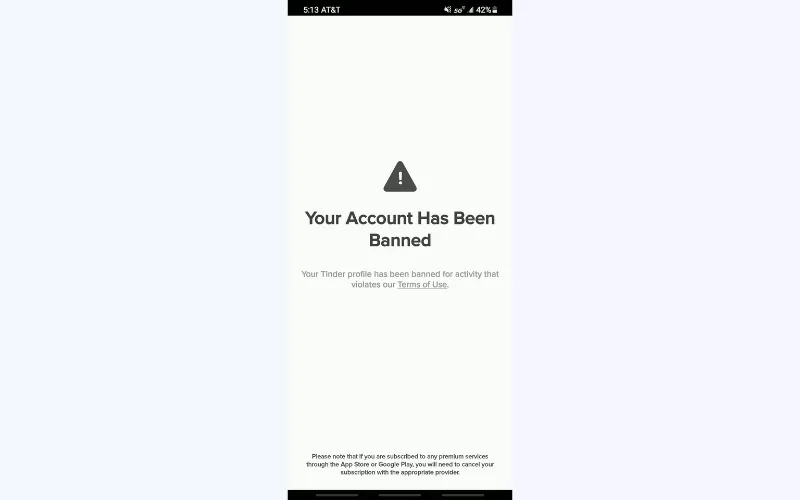
- Create a new account. Some websites may limit your access due to a ban imposed on your account. For instance, you can get banned on social media platforms like Facebook, Instagram, Reddit, or Tinder. Usually, websites block users who violate the site’s rules. But sometimes users get banned by mistake or without a fair reason. Creating a new account may solve this issue. But on some sites, you will also need a VPN to get unbanned.
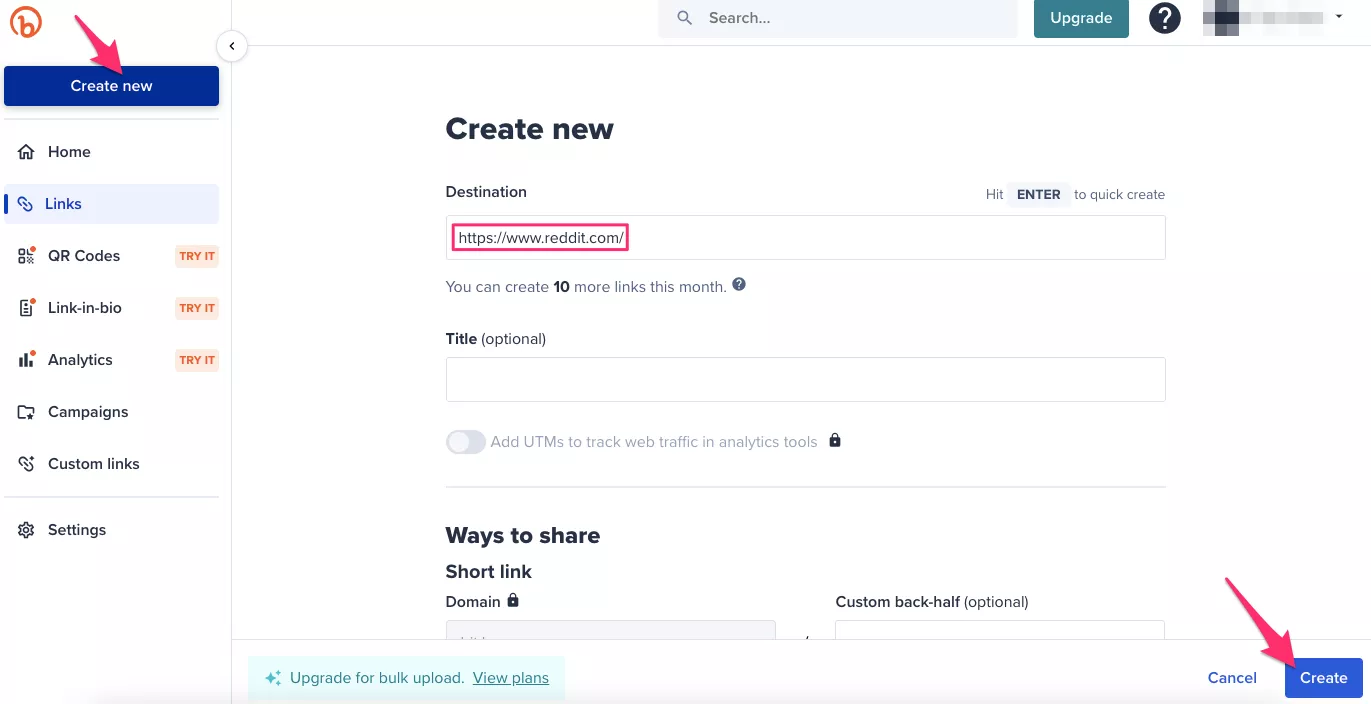
- Shorten the URL. If you’re dealing with a simple URL ban, you can also try to access the site with the help of a URL shortener (the most popular example of such a tool is Bitly). While changing the URL itself, it still links you to the same website, which may help you overcome simple blocks.
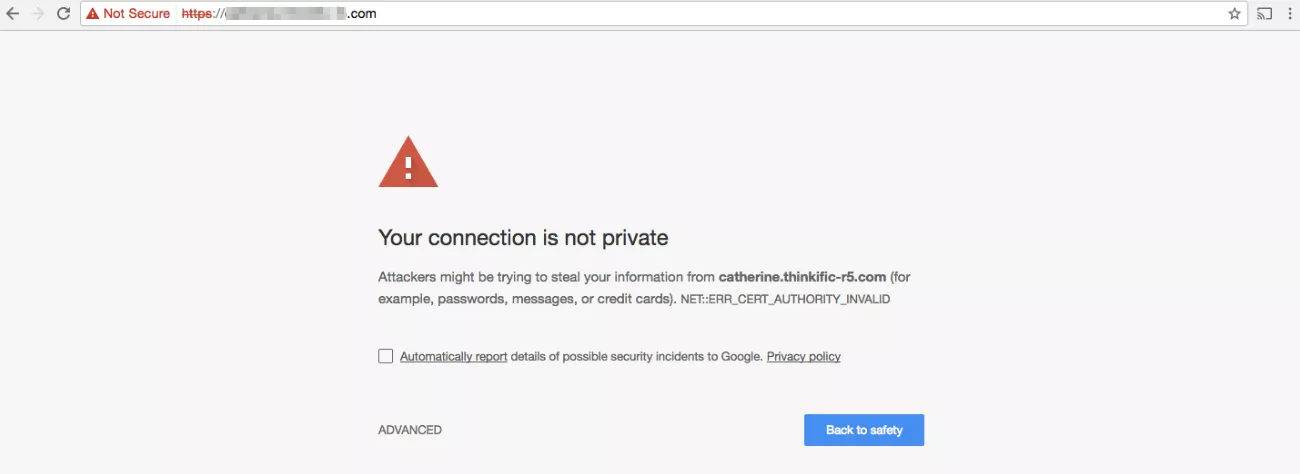
- Add HTTPS to the URL. HTTP or HTTPS is the essential connection protocol every URL begins with. Changing one to another may help you overcome some basic website blocks. But we don’t recommend switching from HTTPS to HTTP because of security concerns. HTTP websites lack encryption, putting your personal data at risk.
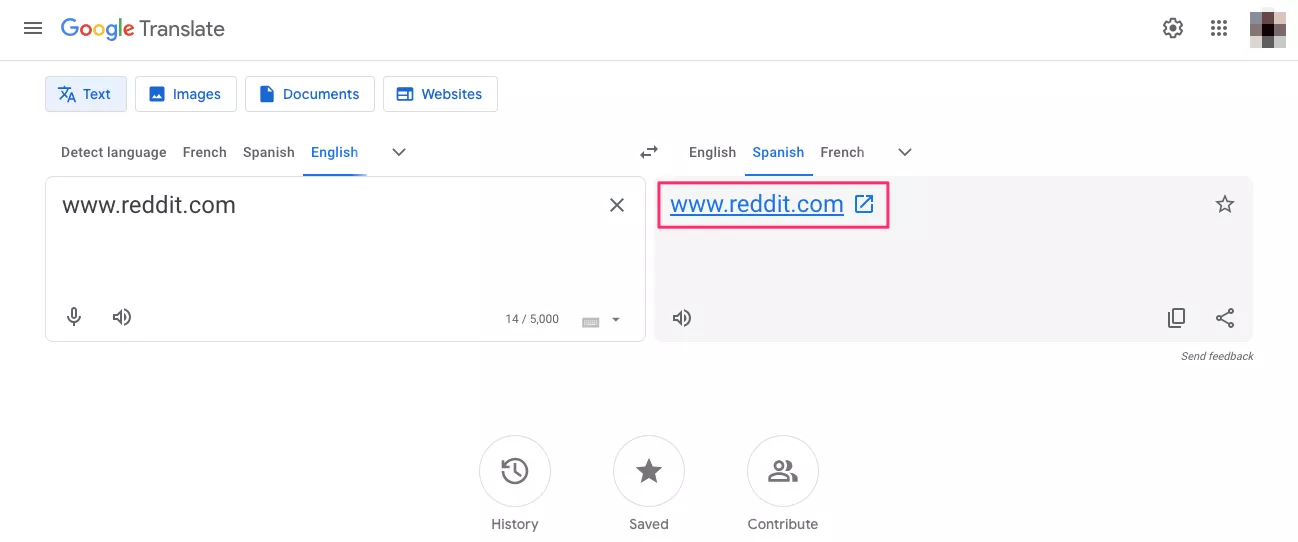
- Insert the URL into Google Translate. No kidding – Google Translate can actually help you access a blocked website. Just insert the URL into the section where you usually put the text you want to translate. Then, click on the link that appears in the translation section. Theoretically, this will help you access the site (but note that this is an interesting trick to try rather than a proven method to unblock websites).
- Restart your Wi-Fi router. When you restart the router, your Internet service provider (ISP) provides you with a new IP address. This simple move can help you unblock a website that blacklisted your IP. But it will only work for you if you have a dynamic IP address. Users with static IP will get the same address even after restarting the router.
Now that you’re familiar with the simplest and most effective methods of unblocking websites, let’s figure out how to choose the most suitable one for your situation.
How to unblock websites from your current location
Here’s how to access blocked sites depending on your location and the specifics of the blocked content.
How to unblock websites at home
If you’re at home and some website is blocked for you, you’re likely dealing with content restrictions imposed by your ISP. It may be due to censorship or copyright limitations. Here, simple tricks like URL shortening and Google Translate won’t suffice. Your best bet is to use a VPN that will change your IP address and run your traffic through another location, where this website is available.
Best solutions:
How to unblock websites at school
School Wi-Fi administrators block websites using less advanced techniques than governments and ISPs. Still, a VPN is a much more reliable option to overcome limitations than unverified proxies and browser extensions. At the same time, setting up a VPN on a school computer might be challenging. That said, we suggest turning to a VPN browser extension. Also, consider installing the app on your mobile device to unblock sites at school without using local computers.
Best solutions:
How to unblock websites at work
You cannot also install a VPN on your work machine when you are limited to Wi-Fi. In addition, your employer can also stop you installing third-party browser extensions, using proxies and Tor. You can work around those restrictions on your mobile phone or tablet. VeePN is available on both Android and iOS, so you can unblock websites at work by changing your virtual location in seconds.
Best solutions:
How to unblock websites when traveling
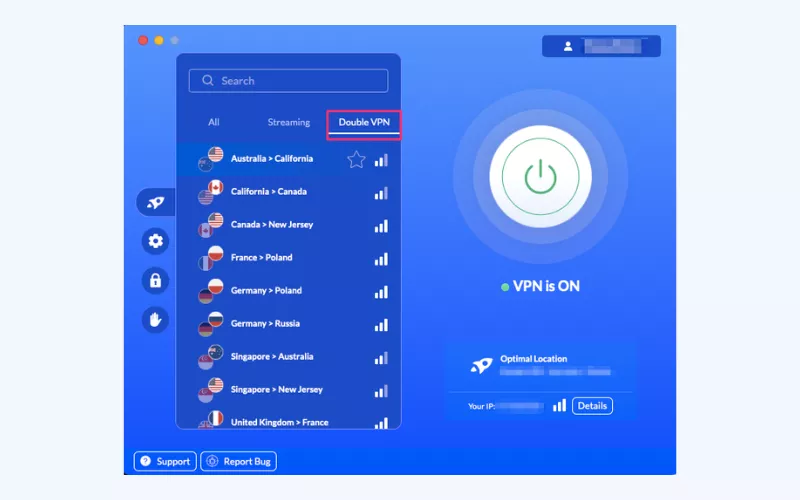
When you go to a country with strict Internet censorship, always make sure to download and install a reliable VPN app on your device in advance. Also, if you deal with confidential information in countries with totalitarian or authoritarian governments, ensure your chosen VPN comes with the Double VPN feature for enhanced privacy. Another beneficial tool for anonymous communication is Tor.
For more details, check out our recent article about using a VPN when traveling.
Best solutions:
- VPN for any preferred device
- Tor
It’s easy to bypass website restrictions and blocks of any complexity with a reliable VPN service provider like VeePN. It comes with all the essential privacy and security features and offers a vast network of servers in 89 locations worldwide. Here‘s how to set up VeePN to unblock any websites of your choice.
How to set up a VPN to unblock websites
Take the following steps to get started with VeePN and access your favorite websites:
How to unblock websites on PC
Follow these instructions to unblock sites online on your computer:
- Pick the preferred VeePN pricing plan and subscribe.
- Download and install the VeePN app on your Windows, macOS, or Linux device. You can use the app on up to 10 devices simultaneously with a single subscription plan – no extra fee required.
- Open the app and connect to the desired server location. VeePN comes with over 2,500 stable and reliable servers in the US, the UK, Canada, Australia, Germany, Italy, Spain, UAE, India, Japan, Hong Kong, and more.

- Configure additional privacy and security features in the app’s settings.
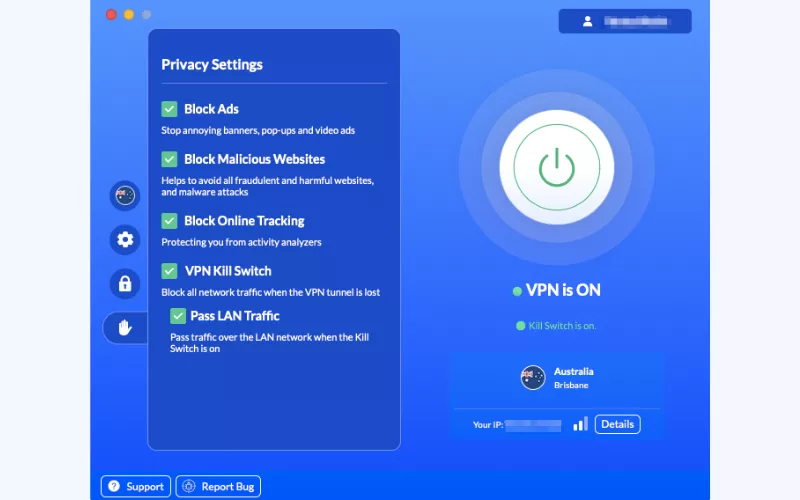
💡 Pro tip: If you need an extra security layer when unblocking a censored website, use VeePN’s Double VPN feature. It will let you route your data through two remote locations, making it impossible for third parties to find out what you’re up to online.
- Turn VeePN to change your IP address and virtual location.
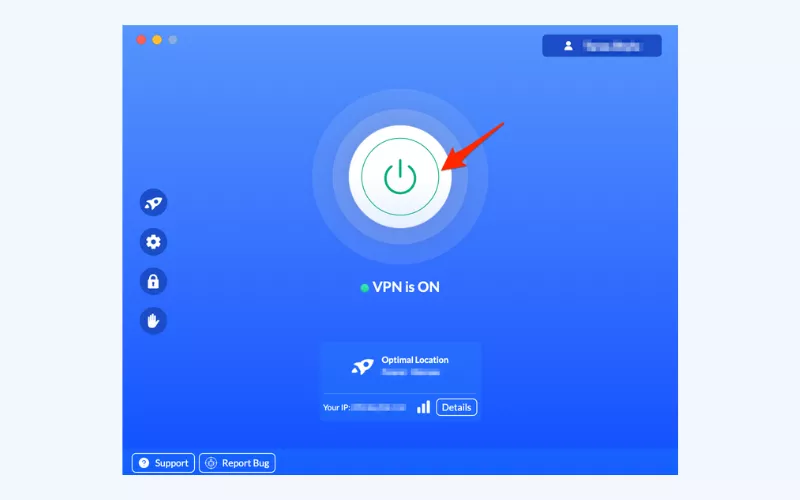
- All set! Open the website of your choice and browse freely.
How to unblock websites on iPhone or Android
Here’s how to unblock websites on Android or iPhone with a VPN:
- Choose the most suitable VeePN pricing plan and sign up.
- Download and install VeePN on your mobile device. Please note that VeePN is available on iOS 15 or higher and Android 13, 12, 11, 10, Pie, Oreo & Nougat.
- Open the VeePN app.
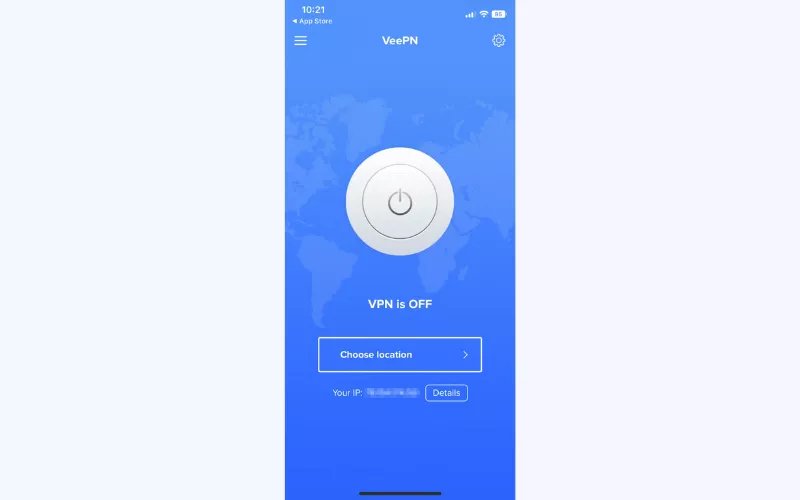
- Allow the app to add VPN configurations to your device.
- Connect to the server location of your choice, be it Argentina, South Korea, France, Turkey, Singapore, or else.
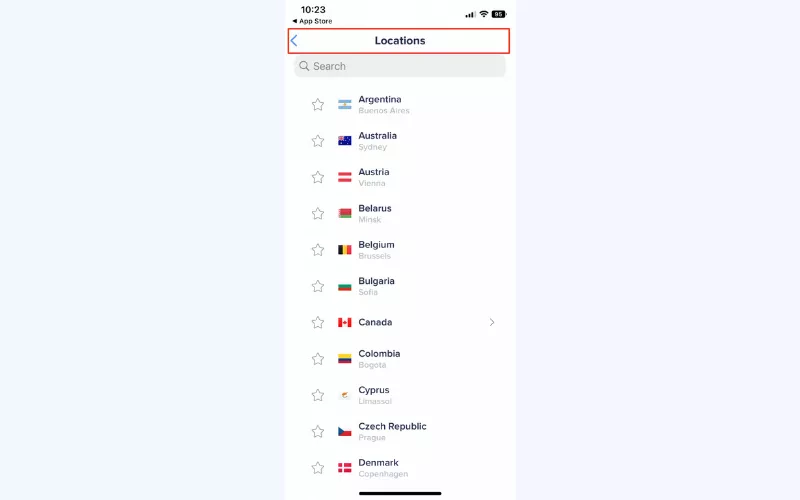
- Turn VeePN on.
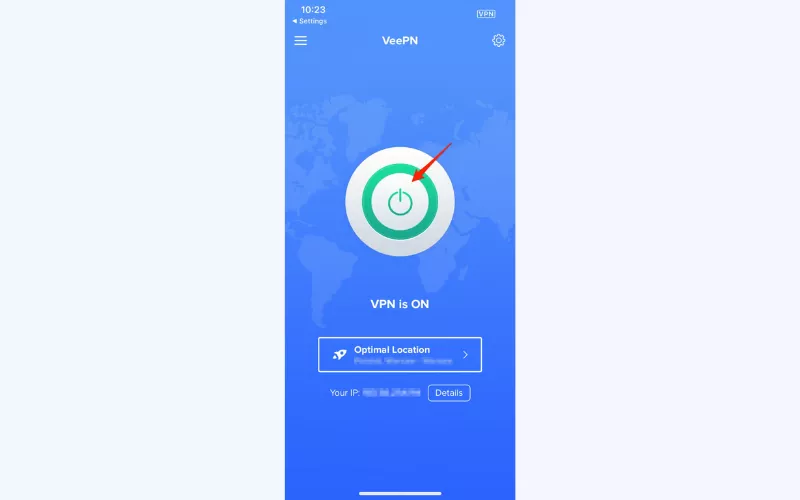
- Done! Head to your chosen website and access it trouble-free.
OK, now you know how to access websites with the help of a VPN and other simple methods. But why are those sites blocked, in the first place?
Main reasons why some websites are blocked
A website might be unavailable to you for different reasons. Let’s discuss the most common ones in more detail.
Security risks
In many cases, websites get blocked when they are considered dangerous or inappropriate. For example, schools and other educational institutions may restrict access to certain sites to keep minors away from harmful or illicit content. The same applies to websites associated with malicious activity, from online piracy to phishing attacks and malware distribution.
Got a critical security alert on Google? Find out how to deal with it in our recent article.
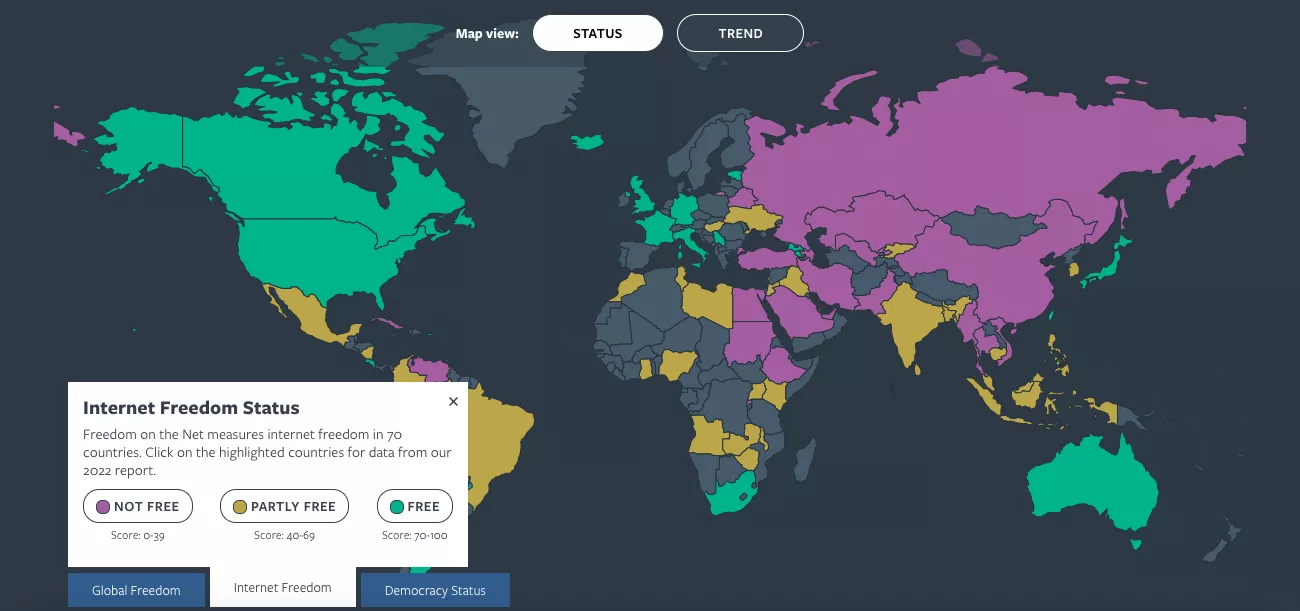
Online censorship
As said, online censorship is one of the most common reasons why websites are blocked in countries with a low level of Internet freedom. In many regions, you won’t be able to access the following types of content:
- Social media sites like Facebook, Instagram, Twitter (now X), Snapchat, Tinder, Reddit
- Streaming services like Netflix, Amazon Prime, YouTube, Spotify
- News websites like BBC News, CNN, The Associated Press, Wall Street Journal
- Human rights websites like Amnesty International, Reporters Without Borders
According to the latest report by Freedom House, the countries with the tightest grip on the Internet include China, Iran, Vietnam, North Korea, Russia, Saudi Arabia, UAE, Pakistan, and Egypt.
Copyright limitations
Some types of content, including your favorite movies, shows, songs, and live streams, may not be available in your country because of copyright and distribution agreements. For instance, some Netflix shows you can watch in most European countries aren’t included in the service’s US catalog. That’s because the rights to distribute this content belong to some other service or network in that region. In some cases, the entire websites are blocked in certain countries (for example, you can access Hulu, Max, ESPN+, and YouTube TV only in the US).
Restrictions at school and work
Again, if a certain website doesn’t work at school or work, local Wi-Fi administrators are responsible for that. Usually, they do it to prevent students or employees from distracting. So websites commonly blocked at school or work are the ones associated with entertainment (from Instagram and TikTok to Netflix and World of Warcraft). Are those bans fair? That’s up to you to decide – but anyway, there’s nothing wrong with watching a YouTube video during a lunch break or checking your social media feed after classes.
Now that we’ve clarified the reasons why your favorite websites may be blocked, another important question arises: can you face any legal issues when accessing websites with the help of a VPN or other unblocking software?
Is it legal to unblock websites with a VPN?
Using a VPN to access online content is legal in most parts of the world with some rare exceptions. But remember to check whether there are any restrictions in your particular country before doing anything potentially questionable. Please be informed that if some action is illegal without using a VPN, it will also be illegal with its use.
With that being said, if you unblock sites at work or watch your favorite show when traveling, it won’t cause any legal trouble (although it might be against the policy of your work, school, or a specific streaming platform).
Disclaimer: VeePN is the VPN service not intended to be used for bypassing copyright regulations or other illegal behavior. For more details, please read the VeePN Terms of Service.
Need to unblock a website? – Try VeePN!
Looking for a top-notch solution to unblock the desired websites wherever you are? Consider VeePN – a reputable VPN service that comes with all the essential features to enhance your privacy, security, and browsing freedom. Connect to one of 2,500 servers across 89 locations in 60 countries worldwide and enjoy the content of your choice without frustrating blocks, connection lags, and Internet safety concerns.
Get an anonymous IP address, protect your digital identity from unwanted snooping, and access any content you want with VeePN. Watch TV shows, stream music, play online games, and surf the web with peace of mind – all without compromising your connection quality. Try VeePN now with a 30-day money-back guarantee!
FAQ: How to unblock a website
There are numerous methods to unblock websites, including proxy servers, the Tor browser, HTML to PDF converters, and browser shorteners. But the most effective way to overcome Internet limitations, including advanced censorship techniques and ISP blocks, is a reliable VPN like VeePN. It changes your IP address, allowing you to browse the web as if you were somewhere else, and encrypts your connection.
Yes! A VPN is a great solution to unblock websites at work, at school, on public Wi-Fi, and even when traveling. When connected to a remote VPN server, you get an anonymous address, which also makes your online presence more private and secure. Check out this article to learn more.
To unblock a certain site on Google Chrome, you can install a VPN app on your device or set up a VPN browser extension for Chrome from the Chrome web store. These tools are designed to overcome Internet limitations and protect your data from various risks. Read this article for more info.
If a certain website is blocked for you, there are a couple of ways to overcome this challenge, including the following ones:
- Use a VPN app or browser extension
- Use a proxy server
- Use the Tor browser
- Change URL to IP address
- Convert HTML into PDF
- Open the cached version of the site
The effectiveness of these methods depends on the reasons behind the limitations you’re dealing with. A VPN like VeePN is the most powerful tool that allows you to bypass any type of limitations, from ISP blocks to firewalls and other censorship techniques.
There are several possible ways to prevent users from accessing a particular website. Here are the most common ones:
- IP blocking – your ISP or the service itself blocks users from accessing censored content.
- Geoblocking – online services, such as streaming platforms and gaming sites, are blocked in some regions due to copyright restrictions.
- Account bans – a website or platform blacklists users that violated its terms of service.
- Firewalls – some sites can be entirely blocked because of security concerns or online censorship.
VeePN is freedom
Download VeePN Client for All Platforms
Enjoy a smooth VPN experience anywhere, anytime. No matter the device you have — phone or laptop, tablet or router — VeePN’s next-gen data protection and ultra-fast speeds will cover all of them.
Download for PC Download for Mac IOS and Android App
IOS and Android App
Want secure browsing while reading this?
See the difference for yourself - Try VeePN PRO for 3-days for $1, no risk, no pressure.
Start My $1 TrialThen VeePN PRO 1-year plan







