What Privacy-Conscious Users Should Know About Encrypted SNI
Did you know that your online privacy can be compromised as soon as you request the server to enter a particular website? The thing is that the TLS 1.3 security protocol, which is supposed to protect your data from being tracked, lacks encryption at the very beginning of client-server communication. This is due to the SNI TLS extension that helps access websites with the same IPs, yet lessens users’ security at the same time. When SNI is exposed, third parties such as ISPs and firewalls can track users and compromise the privacy of internet users by monitoring which websites they visit.
Luckily, there is a solution to this issue called encrypted SNI (ESNI). By encrypting the SNI, ESNI provides an additional encryption layer to keep your data away from hackers, censors, and online snoopers, helping to prevent tracking and protect the privacy of internet users. But how does ESNI work exactly and is it enough to ensure your anonymity? Read on to find out.

What is SNI?
First of all, let’s cover the basics and explain the SNI meaning.
Server Name Indication (SNI) is an extension to the transport layer security (TLS) protocol which specifies a hostname in the TLS handshake. Simply put, the core purpose of SNI is to address the problem of accessing websites hosted on the same server and having the same IPs. SNI allows a single server or web server to host multiple domains and multiple sites on a single IP address by presenting the right server certificate for each SNI host.
The mismatch between the common name or domain name of a website and an SSL certificate results in a “Your connection is not private” error. Web servers use multiple TLS certificates to serve different domains securely.
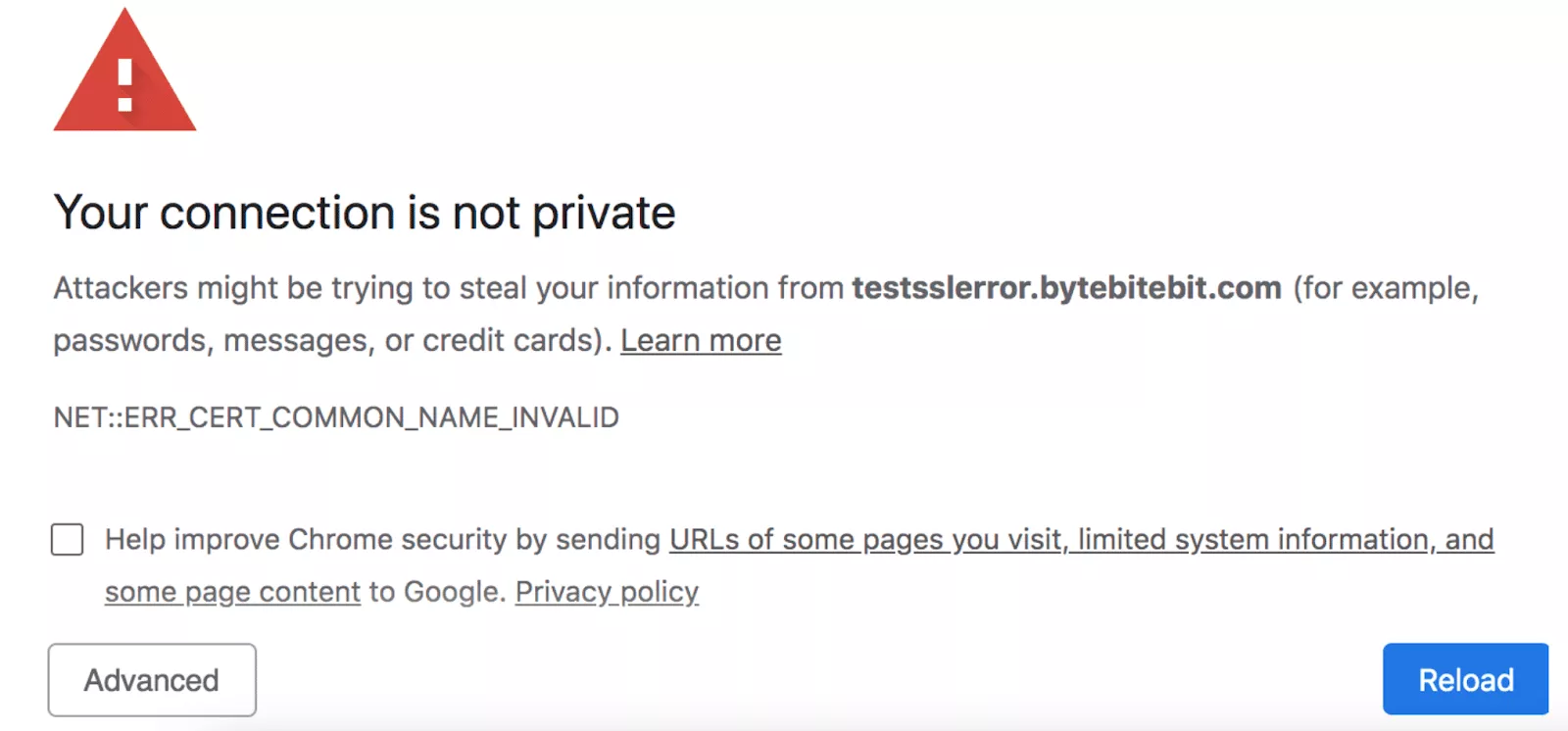
SNI helps avoid this error by enabling secure connections for multiple domains and multiple sites on a single server. It streamlines the communication between a client’s device and a server hosting multiple websites with different domain names. But how exactly does it work, and what does it have to do with your privacy? Let’s clear things up.
When it comes to privacy, connections established using SNI can still expose information if not encrypted.
How does SNI work?
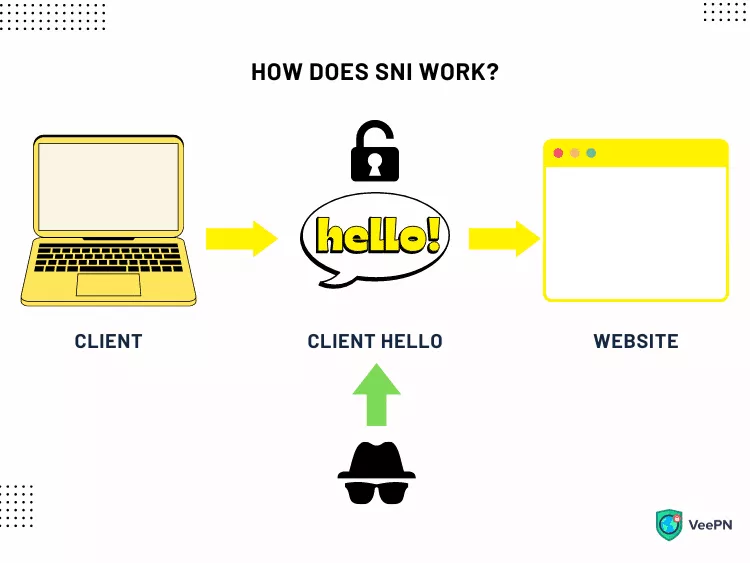
When a user’s device is sending a request to a server, their communication starts with the TLS handshake. This is the process of exchanging certain messages between the two parties involved. At the very beginning, the client sends a clienthello message as the first message in the handshake, which includes the SNI extension in plaintext. At this point, they verify each other, arrange the cryptographic algorithms, and adjust session keys. And here comes the SNI extension. It makes the hostname known at the beginning of the TLS process, called Client Hello, not afterward. As a result, there is no mismatch between your request and the website’s domain name.
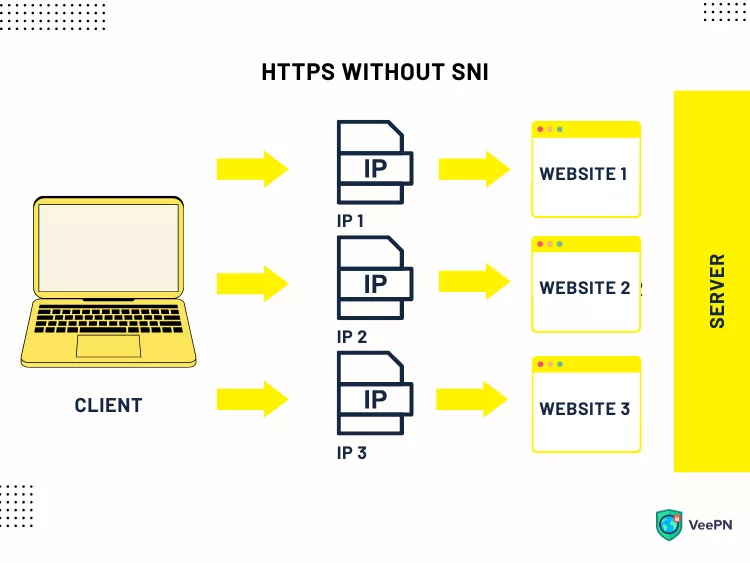
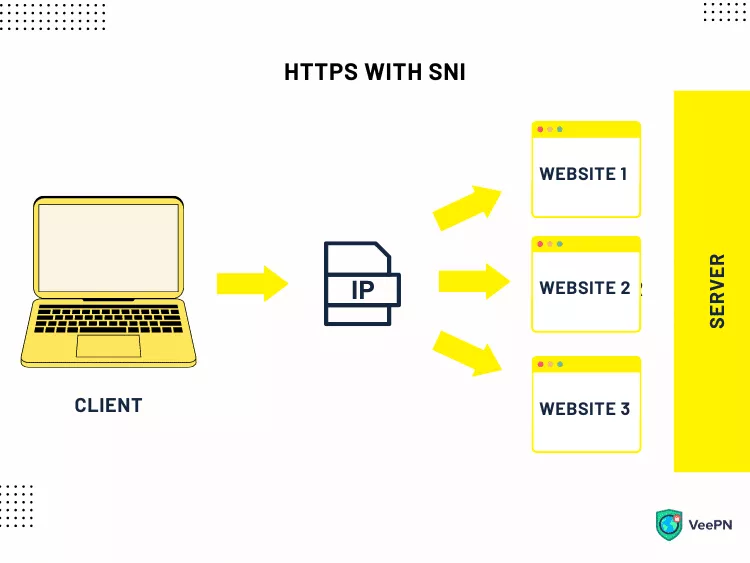
For example, you want to enter https://www.examplewebsite.com, which is hosted on the same IP address as https://www.anotherwebsite.com, https://www.examplewebsite.io, and some others. Thanks to the SNI extension, the connection will be instantly established, although the website’s name doesn’t match the SSL certificate name.
However, while SNI solves one of the most significant TLS issues, it causes another one instead. The initial phase of the TLS handshake lacks encryption, so the SNI part of the message is visible in plaintext during the initial handshake, compromising users’ privacy. Fortunately, you can overcome this challenge with the encrypted SNI.
What is encrypted SNI (ESNI)?
Now, when you know what SNI is and how it works, let’s clarify the meaning of encrypted SNI.
Encrypted server name indication (encrypted SNI or ESNI) is an additional feature of the SNI extension aimed at securing the initial phase of the TLS handshake. The original SNI extension did not provide encryption, and encrypted SNI is only supported in newer TLS versions, such as TLS version 1.3 and above.
Without SNI encryption, hackers can use various techniques, such as phishing or man-in-the-middle (MITM) attacks, to trick users, steal sensitive information, or redirect them to malicious websites. And that is the main reason why ESNI was created. Previous versions of TLS did not support encrypted SNI, and only TLS version 1.3 and above, when used with a compatible TLS server, can provide this feature. It’s set to secure SNI as the most vulnerable stage of the TLS process, preventing online snoopers and third parties from spotting clients’ requests at the Client Hello.
Let’s look at how secure SNI works in more detail.
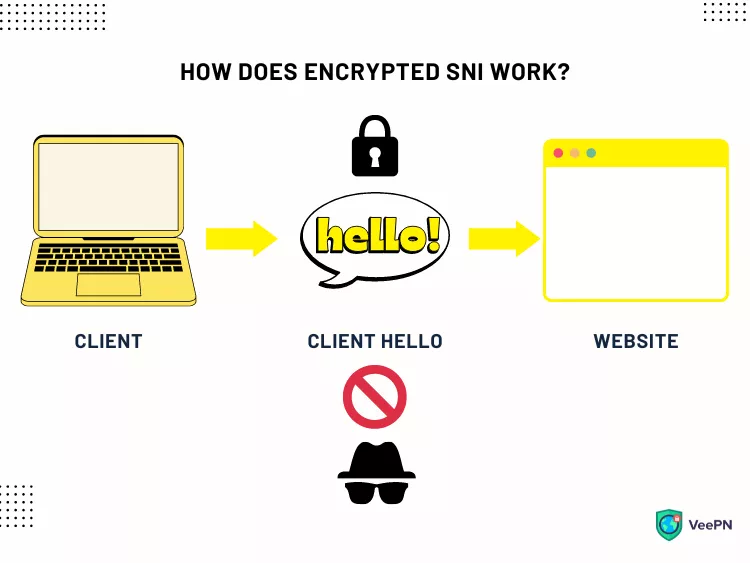
How does encrypted SNI work?
The key goal of encrypted SNI is to secure the connection between a client’s device and a server at the very beginning of their communication. The problem is that at the Client Hello stage, the TLS encryption keys aren’t yet approved.
To eliminate this vulnerability, encrypted SNI provides an alternative solution—a public key attached to the DNS record. DNS records are used to retrieve the public key needed for encrypting the SNI part of the handshake, ensuring that only the intended server can decrypt it. This approach helps verify and secure the connection before the TLS protocol encrypts a user query. A client uses a public key that encrypts the SNI record, which can then be decrypted only by the relevant server.
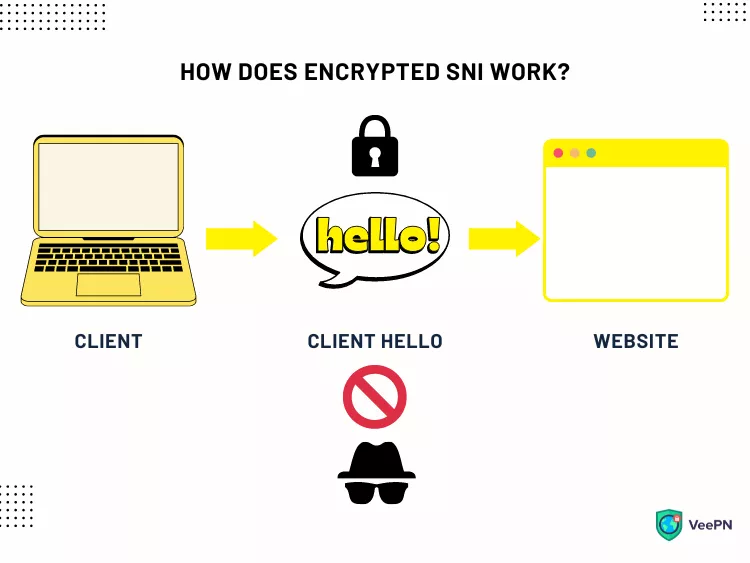
To be more precise, here’s how exactly SNI encryption works:
- A user’s device sends a request to a DNS server to discover the site’s IP address. The DNS records may also include the public key required for encrypting the SNI part of the handshake.
- The DNS server’s response includes the website’s IP address and encrypted public key.
- The device sends a Client Hello request to the IP address, and the client encrypts the SNI part of the clienthello message using the public key from the DNS records.
- The backend server is responsible for decrypting the encrypted SNI and establishing a secure connection to the desired website.
- The server delivers the website’s TLS certificate.
- During the TLS handshake, the cipher suite is negotiated as part of the encrypted client hello. The encrypted client hello (ECH) extension is designed to protect the SNI and other sensitive information during the handshake. ECH encrypts the entire clienthello message, providing enhanced privacy so that no third parties can monitor the user’s current activity.
Unfortunately, SNI encryption is currently not supported by most web services and browsers. Some rare exceptions are Mozilla Firefox and Cloudflare. As for the most common uses of ESNI, it doesn’t only protect from nosy snoopers, but is also one of the most widespread approaches to resisting online censorship.
How encrypted SNI helps avoid censorship
Online freedom is one of the greatest concerns these days. According to the Freedom House, only eighteen countries have free access to the global web. Governments of totalitarian and authoritarian states strive to control the browsing activities to prevent people from viewing international resources and communicating via social networks or messengers.
In particular, online censors use SNI as the most vulnerable part of the TLS 1.3 encryption to determine users’ online activities and limit their access to certain content. At the Client Hellostage, censors, along with other third parties, can easily detect which server a person is trying to access and block it.
And that’s where Encrypted SNI comes to the rescue. It provides more Internet freedom by protecting every single stage of the user’s request to the server and hiding their traffic from Internet service providers (ISPs) and other third parties. However, to be completely reliable, ESNI can be empowered with some additional security measures.
What else do you need to stay private with encrypted SNI?
Except for ESNI itself, some additional security protocols will help you avoid unwanted monitoring even more effectively. Let’s take a closer look at the most important ones.
DNS over HTTPS (DoH) protocol
Even if you’re using ESNI, meticulous snoopers can still find a way to take a peek at your traffic. So it’s worth getting an extra security layer such as DNS over HTTPS protocol (DoH), which runs DNS queries through an additional HTTPS encryption session.
DNS over TLS (DoT) protocol
DNS over TLS (DoT) is another powerful network security protocol that encrypts DNS queries and responses through the TLS protocol.
Domain Name System Security Extensions (DNSSEC)
This set of specifications strengthens DNS protocols by ensuring cryptographic SNI authentication of responses coming from authoritative DNS servers. With the help of DNSSEC, you can enhance your protection against various cyber threats, such as DNS spoofing and hijacking.
Other ways to enhance your online privacy
If you’re striving to complete anonymity when surfing the web, there are many alternative ways to make your online activities invisible and well-protected. In addition to encrypted SNI with DoH, DoT, and DNSSEC protocols, you may consider the following Internet privacy tips.
1. Choose the most private browser
Many aspects of your online anonymity depend on the chosen browser. And guess what? The most popular browsers, such as Google Chrome, Microsoft Edge, and Safari, lack many important security features. At the same time, some less-known options can better protect you from third-party monitoring. To name a few, these are Ungoogled Chromium, Iridium, LibreWolf, Brave, Mozilla Firefox, and The Tor Browser.
2. Use a proxy server
You can also hide your online activities by spoofing your IP address and rerouting your traffic to a proxy server. However, while being quite effective for bypassing certain online limitations, proxy servers cannot fully protect your identity since they do not encrypt your connection. As a result, a proxy won’t keep you away from viruses and other cyber threats.
3. Protect yourself with a VPN
When it comes to private browsing and online security, a virtual private network (VPN) is probably the most powerful solution. A reliable VPN service can help you stay completely anonymous since your data travels through an encrypted tunnel and cannot be compromised by third parties. In general, VPN tools are focused on the following purposes:
- Hiding your IP address to make your online presence invisible to third parties
- Providing privacy and security features to protect your personal data from various cyber threats, including MITM attacks, phishing, and DDoS attacks
- Ensuring access to the free Internet and fighting against online censorship
Want to stay secure online? Try VeePN! It’s a trustworthy VPN service that protects your data thanks to the most powerful AES-256 encryption protocol. On top of that, VeePN provides the NetGuard feature to keep you safe from online trackers, intrusive ads, and third-party monitoring. And, if your VPN connection suddenly fails, VeePN will ensure no sensitive data will be lost with the help of the KillSwitch feature.
FAQ
Server Name Indication (SNI) is a TLS security protocol extension that helps avoid hostname mismatch in the TLS handshake. It streamlines the communication between a client device and a server by revealing the hostname at the initial Client Hello stage. However, this TLS phase lacks encryption and is vulnerable to third-party monitoring.
Encrypted SNI (ESNI) is an extra privacy feature securing the Client Hello phase of the TLS handshake. It encrypts SNI extension with the help of a DNS public key. As a result, the communication between a client’s device and a server becomes inaccessible for hackers and online snoopers. For more details, read this article.
Although the SNI extension wasn’t originally added to the TLS 1.3 protocol, it has become its essential component. Without TLS SNI, it’s impossible to run multiple SSL certificates on the same IP address. If TLS 1.3 lacks SNI, your connection to a server will likely be interrupted by a “Your connection is not private” error.
VeePN is freedom
Download VeePN Client for All Platforms
Enjoy a smooth VPN experience anywhere, anytime. No matter the device you have — phone or laptop, tablet or router — VeePN’s next-gen data protection and ultra-fast speeds will cover all of them.
Download for PC Download for Mac IOS and Android App
IOS and Android App
Want secure browsing while reading this?
See the difference for yourself - Try VeePN PRO for 3-days for $1, no risk, no pressure.
Start My $1 TrialThen VeePN PRO 1-year plan







