Does VPN Protect You from Hackers? Types of Hacker Attacks and How to Survive
Everyone online is a target for hackers — one hacker attack happens every 39 seconds. That’s a bitter truth. As a result, the internet is filled with different forms of malware — spyware, scareware, ransomware…So, how should you stay secure on the Internet under constant threats?
A great cybersecurity tool, a virtual private network (VPN), can give you a hand in this regard…or not? Well, that’s what our article is for — for you to find out what a VPN does and doesn’t protect from, as well as to provide you with tips on improving your security online. So, let’s get going.
Can a VPN protect you from hackers?
A VPN isn’t almighty. It can however save you against certain attacks by hackers. Now we can have a closer look at what VPN can and cannot do in terms of hacker attacks.
VPN protection: What hacker attacks are included?
Even though the VPN does not ensure that you will be safe installing malware or clicking on bad links, it does secure you against a few techniques hackers use. Let’s review them.
Man-in-the-middle attacks
The most frequent form of attack is man-in-the-middle (usually on public Wi-Fi) attack, where cybercriminals place themselves into a conversation between a user and an app or a site (i.e., in the middle) to intercept data. In so doing, the hackers will be able to detect any information being transferred between two parties such as account logins and buying transactions, and may gain unauthorized access to your accounts. Identity theft may even be caused by these attacks. Nevertheless, a VPN on your computer will encrypt your web traffic inside an encrypted tunnel, so a hacker will not be able to read your Internet traffic in case they introduce such an attack.
Distributed denial of service (DDoS) attacks
These types of attacks involve someone sending a lot of empty data to overload and crash the service. Cybercriminals often do it to make your connection unusable. The thing is, though, that they need your real IP address to do so. Accordingly, using a VPN is a life-saver here, as it’ll handle IP address masking and hide your actual IP address from attackers.
Session hijacking
Or cookie theft — once again, common when you use public Wi-Fi — is when hackers try to take over a user’s session to get their session ID and then impersonate that user on network services. For example, this may happen while you’re purchasing something online. So, to get your data encrypted with secure protocols, make sure you use a VPN when connecting to random hotspots.
Fake WAP
Where WAP stands for wireless access point. And it’s basically when hackers create fake Wi-Fi hotspots without passwords, something like “Free McDonald’s Wi-Fi,” to lure people who need immediate internet access. These hotspots threaten your security — when you connect to one such WAP, cybercriminals will be able to see your data traveling through their network. At the same time, a VPN encrypts your data, so the hacker won’t get the chance to access any personal information and you keep more secure access to your accounts.
VPN protection: What hacker attacks AREN’T included?
There are some limits to what a VPN can do, nevertheless. While VPNs are meant to protect your data when it’s in transit as part of your overall VPN security, some hacking attacks surpass it. So let’s check out in which cases a VPN won’t be of much help for you.
Human mistakes
It is sad to note that even the most effective cybersecurity tool in the market will not save you. To give an example, a VPN, even of the highest quality, is unable to protect you, in case you use a suspicious link or a pop-up ad with malware (without knowing or intentionally), that is, without a VPN. So better to have your antivirus software on at all times.
Malware
Keeping you safe from viruses and all other types of malware, in general, isn’t up to a VPN. Malware usually penetrates your device when you accidentally click on a pop-up ad or open a suspicious link. And once it’s infiltrated, a hacker can view your data, even if the VPN encrypted it.
But! Some VPNs do provide a real gem in the form of an ad/malware blocker that alerts you before you access a dangerous site and gets rid of relentless ads (which may carry malware, too, by the way). You can check out VeePN’s NetGuard to see what a malware blocker is all about.
Phishing
A type of social engineering attack that plays on people’s trust. You may have come across a phishing site, for example, which domain is similar in name and appearance to a legit website. Such sites usually have spoofed URLs, like here:
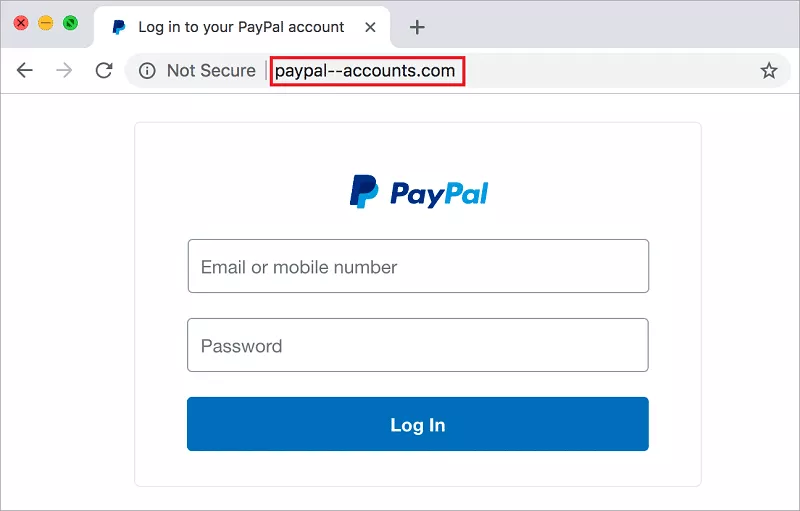
Say you believed that this is a legitimate PayPal website — once you share your user credentials and other sensitive information, there’s nothing a VPN can do as scammers will get past its security features.
Bottom line: How does a VPN protect you?
Long story short — a VPN protects you by encrypting your internet traffic and routing it through a VPN server, sitting between your Internet connection and the wider web. This way, it masks your real IP address and helps prevent third parties like your Internet service provider from tracking you.
That one’s settled. But we feel like you must have other questions along the way. So, let’s get on with some of them.
Can a VPN be hacked?
Another important question you may have been asking yourself. Although top VPNs provide bank-level encryption and many security benefits, even paid VPN providers can’t fully stop a hacker from reaching your VPN app if you overshare data or trust shady services that might sell user data. For instance, in the case of a spyware attack or an exchange of username and password with anyone, a VPN wouldn’t be able to protect you.
What else can protect me against hackers attacks?
Another question is: how can you improve your online security? We’ve compiled a list of what can help you.
- Strong passwords. You need to stop using ordinary weak passwords like your birth date or some other recognizable words and phrases, since hackers can use brute forcing software to look through billions of password combinations until they come across the right one for your account.
- Two-factor authentication (2FA). The 2FA system secures your accounts with two “factors” — your password and the SMS, a face/fingerprint scan, or any other way offered by the system. It means that to gain access to your personal information, a hacker will need your password and your device or, well, you.
- Updating your software. This one is important to keep tabs on — software updates fix security vulnerabilities and help prevent potential exploits. So pay attention to whether your apps or the operating system are updated since the opposite may expose you to cyberattacks.
- Installing VPN on your router. To protect all your devices connected to the home network from some types of cyberattacks, you can just install a VPN on a router. Using a VPN this way will count only for one device, so, with VeePN, you can connect 9 more devices outside your network.
- Antivirus software. It’s also a sound idea to pair your VPN with an antivirus to strengthen your defenses online. An antivirus will detect malicious code on your device and remove it, while some VPNs will detect and block sites that host malware, so it would never reach your device.
How to protect yourself from unwanted hacking attacks online
Finally, can you protect yourself 100% from the attacks? Sadly, no. However, you can always reduce the risks and enjoy your online activity without much fear. Let’s see what steps you can take to make browsing the safest experience for you:
- Follow the updates. What is the latest news in the tech world? What sites were breached? When you know a lot about the vulnerabilities on the web, it’s easier to avoid them.
- Keep track of your passwords. Do you use one password for all web platforms you use? Sure, having only one is much easier to remember. But…it puts your data at huge risk. So you should create different combinations for each different website. On top of that, change passwords from time to time — it should help you feel better about your security on the web.
- Log out of your devices. Sounds easy — log out each time you’re through with your account. It may be annoying, but definitely worth it in the long run.
- Be careful on public Wi-Fi. Free public networks are flooded with vulnerabilities. So what may seem like a lifesaver often turns out to be a threat. In case you desperately need to connect to one, beware of what data you share. For example, you should avoid sensitive transactions like banking, and not share your personal and financial information.
- Use a VPN. Even if VPN services can’t protect you from all hacker attacks, they’re still incredibly useful. A secure VPN from a trustworthy VPN provider encrypts your activity online and secures the traffic, getting you stronger security and enhanced privacy. VeePN is a great way to start securing your online presence — it shields your data with AES-256 encryption and secure protocols, keeps a stable VPN connection and uses a Kill switch if your VPN connection drops, masks your IP address, and offers an effective ad/malware blocker.
After all, the internet realm is dangerous. And with hackers only becoming more inventive, you should always keep an eye out. Cybersecurity is a top priority nowadays. So let’s treat it like one.
FAQ
Do VPNs actually stop hackers?
Yes, VPNs can prevent some hacker attacks, like man-in-the-middle attacks, DDoS attacks, session hijacking, and fake WAPs. Learn more about them in this article.
What will a VPN not protect you from?
VPN’s powers are not limitless. And it won’t protect against phishing attacks, your own mistakes, and all forms of malware (although some VPNs, including VeePN, do offer ad/malware blockers that can protect you against some malware types). Learn more in this article.
VeePN is freedom
Download VeePN Client for All Platforms
Enjoy a smooth VPN experience anywhere, anytime. No matter the device you have — phone or laptop, tablet or router — VeePN’s next-gen data protection and ultra-fast speeds will cover all of them.
Download for PC Download for Mac IOS and Android App
IOS and Android App
Want secure browsing while reading this?
See the difference for yourself - Try VeePN PRO for 3-days for $1, no risk, no pressure.
Start My $1 TrialThen VeePN PRO 1-year plan







