Does Incognito Mode Work? How to Delete Incognito History?
We’ve all been there — looking up some bizarre, embarrassing, cringe-inducing things online. Chances are you don’t want them in your browser where your mom, roommate, boss, or aunt Karen might stumble upon. So, you fire up your browser’s tried-and-true incognito, or private, mode which promises to keep your activity from prying eyes. But you may be shocked to learn how little protection it actually provides. That said, what exactly does incognito mode do and how to delete incognito history? Read along to find out.
What is incognito mode?
Incognito mode is a feature when the browser, be it Chrome browser or any other, automatically erases a record of the web pages you visit. Every browser has a different name for this setting:
Incognito Mode in Chrome
InPrivate Mode in Microsoft Edge
Private Browsing in Safari
Private mode in Firefox
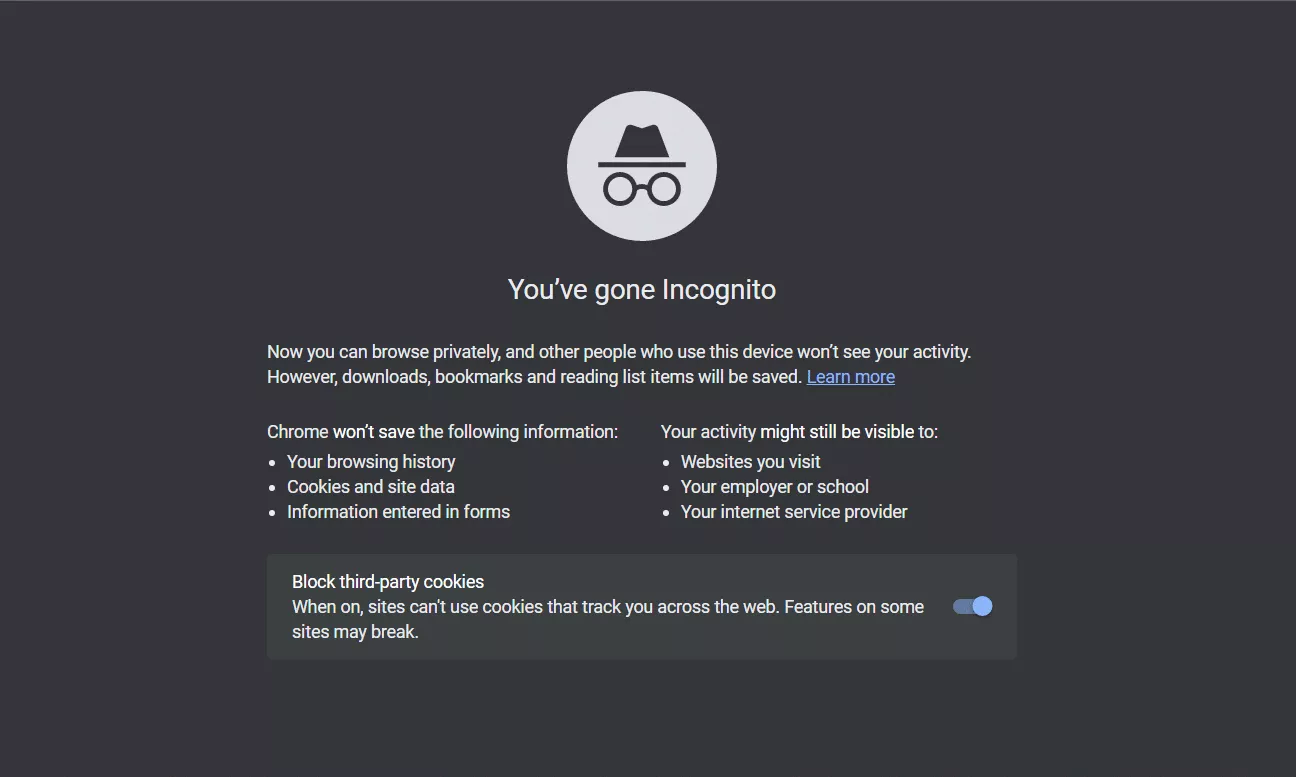
Once you open an incognito tab, your browser starts a new private browsing session — all the cookies and site data saved during this session will be automatically swiped. But regarless what secure web browser you use, it’s important to know what incognito mode can and can’t do.
What does incognito mode do?
When new incognito window opens, it does the following:
- Keeps your browsing history empty
- Deletes browser cache that contains the contents of pages you visit
- Erases cookies that track your web activity
- Blocks third-party cookies unless you choose to allow them
The idea is that once you’re done with your session and you close your browser, all incognito history related to page visits gets automatically deleted making it invisible to the next person who uses the browser. That said, an incognito mode masks your Internet activity from people with physical access to your computer or phone.
Is incognito mode safe?
So, does incognito mode boost your online privacy online? Yep. Does it serve as Harry Potter’s invisibility cloak and hide your identity? That’s a no.
You’ve probably seen the warnings that pop up in incognito mode telling you your employer or Internet Service Provider (ISP) might still be able to keep tabs on your online activity.
How would they do that? You’re supposed to be incognito, right? Well, because incognito mode only affects what’s being stored locally on your device. All of that traffic is still being routed through the servers of your ISP and, perhaps, your school or office when you’re going online there. So it can still be intercepted and tracked. This means that if you really want to anonymize your web traffic, consider using a Virtual Private Network (VPN) to conceal your identity (more on that later).
In addition to ISPs, anyone who has administrator rights for your device, will be able to see your incognito browsing history if they want to.
Using incognito mode comes with other risks:
- Browsers don’t always securely delete any data that you built up during an incognito session. Some of it could still be found within a software recovery program or inside your device’s DNS cache — it matches the URLs of the sites you visit to the IP addresses.
- Things that go wrong on your device can compromise the effectiveness of incognito mode. Since many browsers delete the data from your incognito history, once you close your session, an unexpected error like a computer crash could keep that data from being deleted entirely.
- Any malware or spying software like a keylogger could easily be keeping tabs on your incognito browsing if your device is infected.
This leads us to answer the “What doesn’t incognito mode do?” question in detail.
What doesn’t incognito mode do?
When you first open a browser window in an incognito mode, most browsers warn you of its limitations. Most people skip this part, so let’s spell it out here. An incognito mode doesn’t:
- Prevent web tracking. Your ISP, the government, or network admin at your office or school can still see which websites you visit. Your IP address and web activity can still be tracked.
- Hide your location. Incognito mode doesn’t work out in the web — websites can still see where you are from based on your IP address or GPS.
- Cloak your IP address. Websites you visit can see your IP address and use it to track you.
- Protect your traffic from cybercriminals. Incognito mode’s scope of work is limited here because this feature doesn’t offer any extra security features.
- Delete your browsing history from the DNS cache. As we’ve already mentioned, anyone with extra know-how can locate your incognito mode history on your device.
Now, we’re not trying to scare you or make you think that private browsing is useless. It’s still a great tool and an easy extra layer of security, but you need to know how to delete incognito history. In fact, let’s do a quick recap of when you should use it.
When should you use incognito mode?
There’s definitely no harm in using incognito mode. Because it doesn’t save browsing history, the info you might put into forms on those websites for autofill, or cookies from those websites, an incognito mode is good for:
- Stopping advertisers from snooping (and being annoying). No cookies and site data mean no targeted advertising. The latter can be a real drag if it follows your family members around and shows them which birthday gift you’ve been looking up for them.
- Protecting your web activity on a shared/public computer. Incognito history prevents those who share a computer with you from tracking your online activity. They can’t look up your browsing history or login and site data.
- Using two accounts at the same platforms. You can log in to multiple accounts that only allow one user logged in at a time. This comes in handy when your friend wants to use your device to log in to their accounts or you want to keep your personal and work profiles apart.
- Getting better deals. Some airline or hotel websites may change prices based on your search history. But since incognito mode doesn’t store DNS cache history, those companies can’t hike their prices.
- Discovering different content. When we look for the same thing, it’s a hint to websites that we like this content. So many of them personalize our experience and show us something similar. For example, if you tune into DIY videos on YouTube, you’ll see your homepage filled with various tips. However, since incognito mode doesn’t record your browsing history, the website content you see will update.
So yeah, incognito mode isn’t at all bad or futile, but it’s important to understand its limitations as you can’t fully save incognito history. Remember that just because a browser deletes the information about your session doesn’t mean it’ll keep a determined snoop from finding out what you’ve been up to. You’ll need some stronger tools here to delete history from private browsing.
So now, let’s see how to delete incognito history!
How to delete incognito history on your device
Here’s detailed instructions on how to clear incognito history on various devices:
Windows device
To delete incognito history on Windows device, do the following:
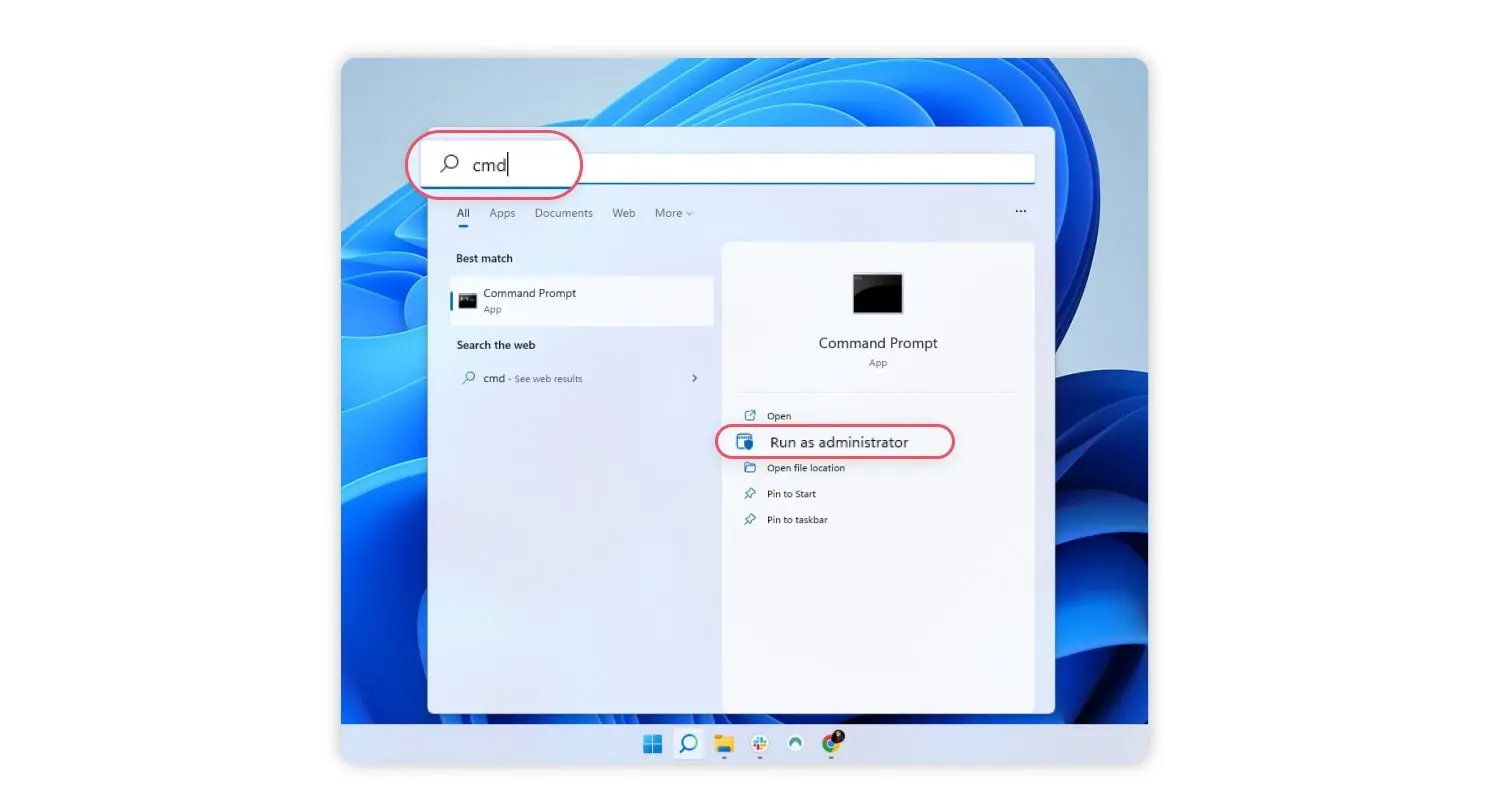
- Find “command prompt” using the Windows search box and choose the “run as administrator” option.

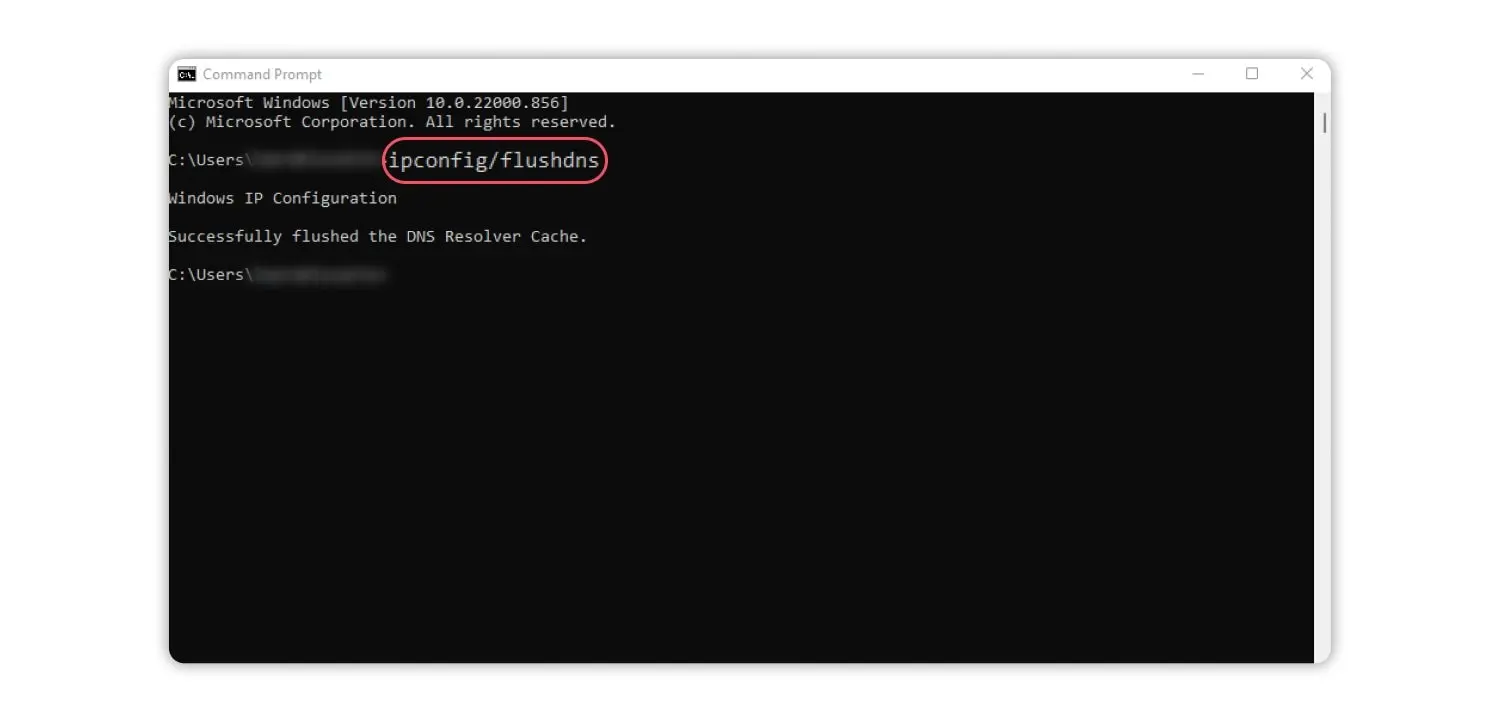
- Type ipconfig /flushdns in the command prompt window and press “enter.”

Mac
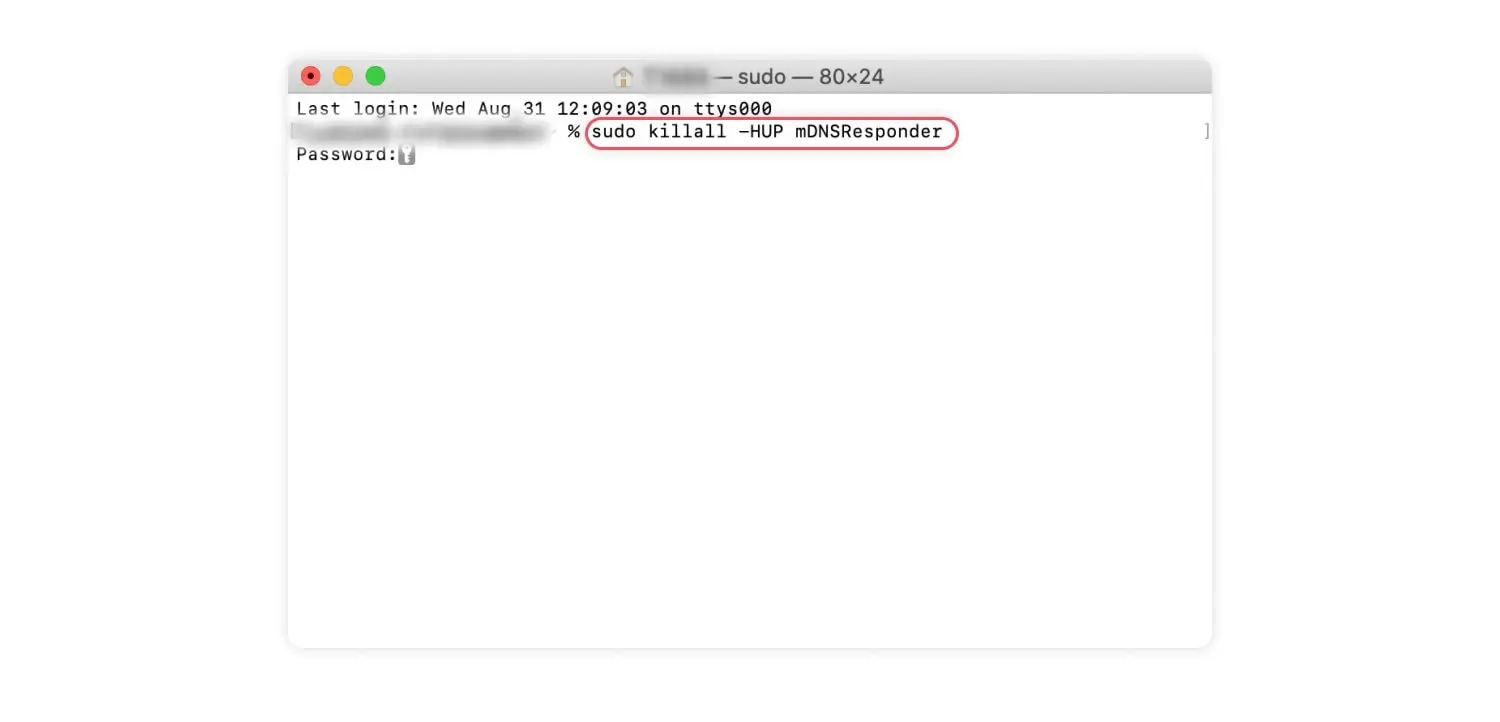
To delete incognito history on Mac, follow these steps:
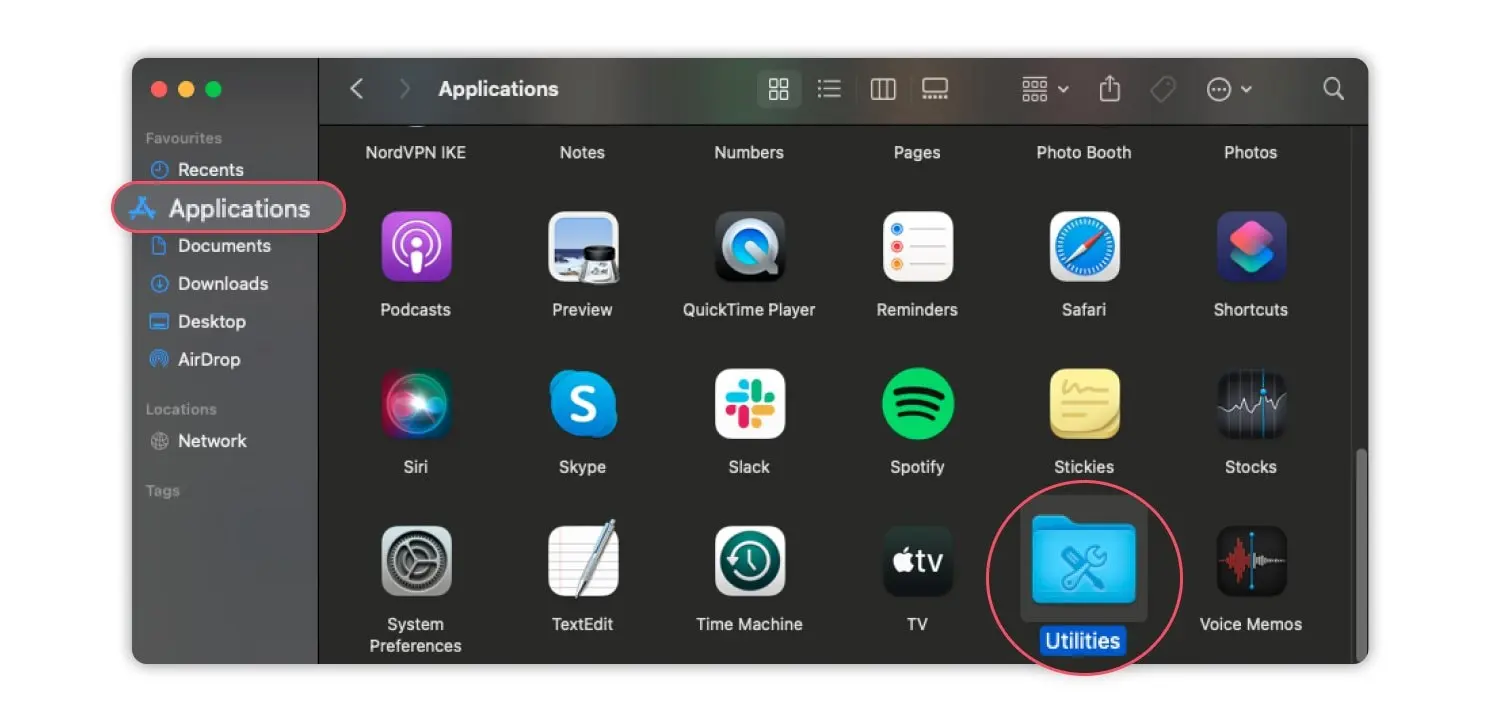
- Open the “applications” folder and choose “utilities.”

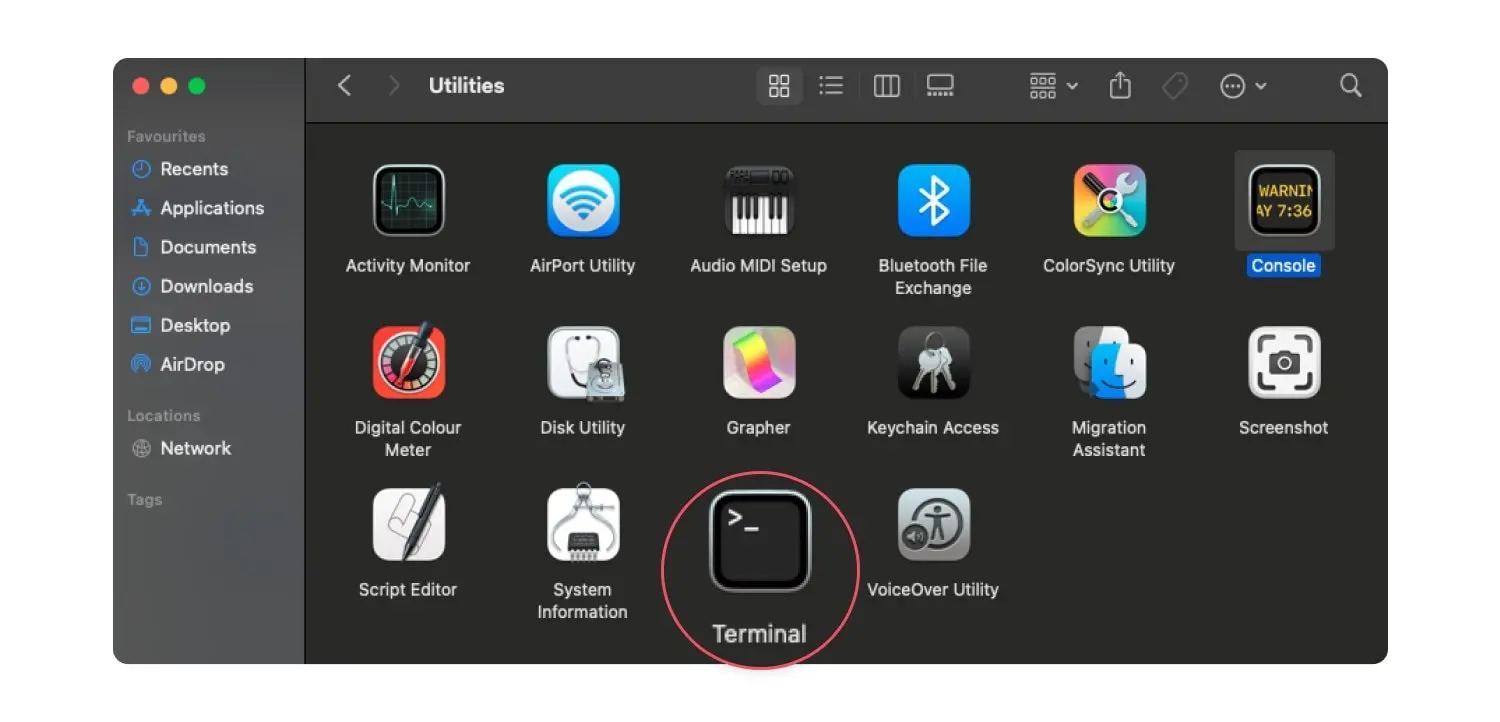
- Doubleclick to open “terminal.”

- Type sudo killall -HUP mDNSResponder in the terminal and press “enter.” You’ll also need to enter your password. Done! All your incognito browsing history has been deleted!

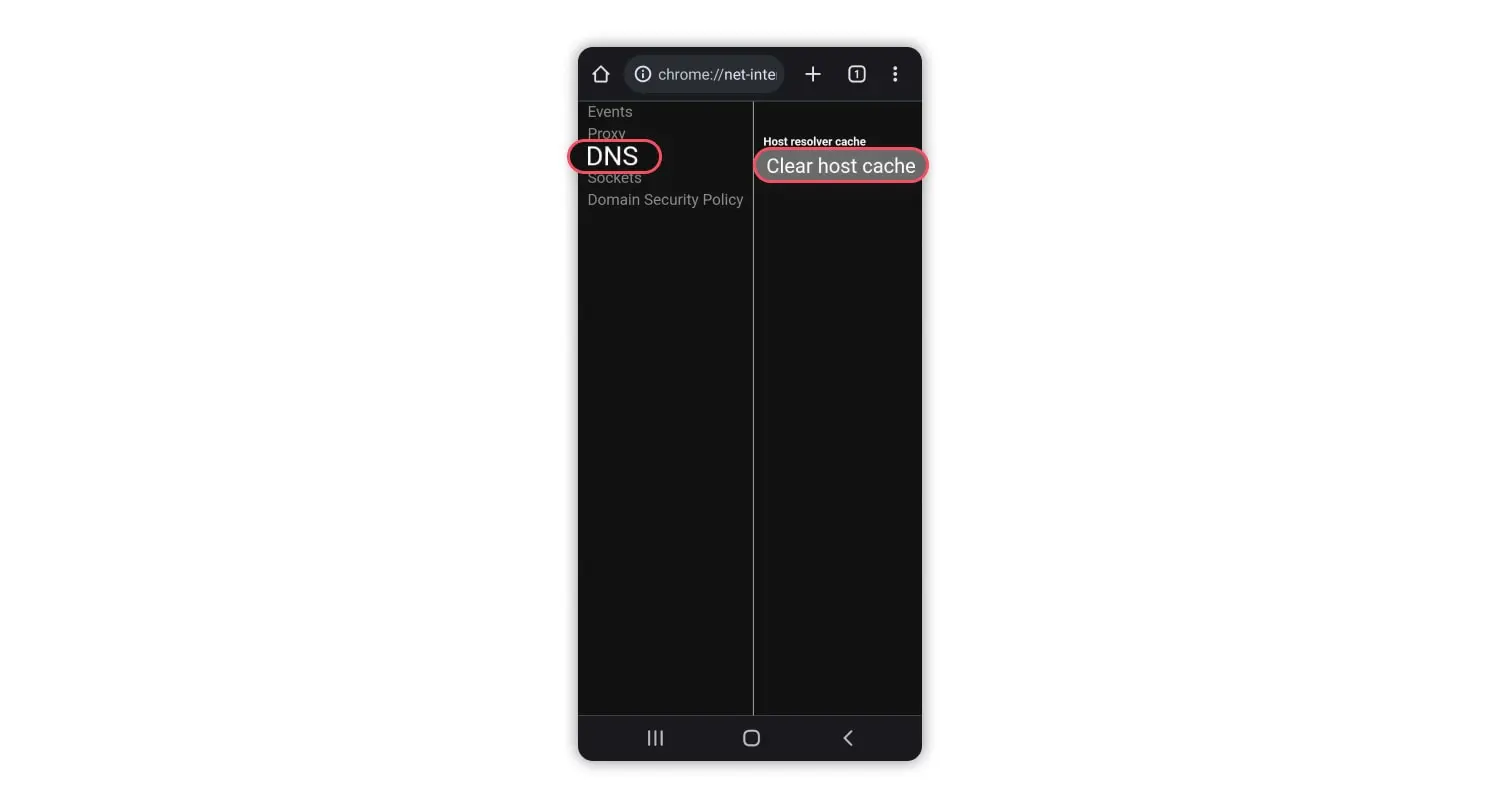
Android
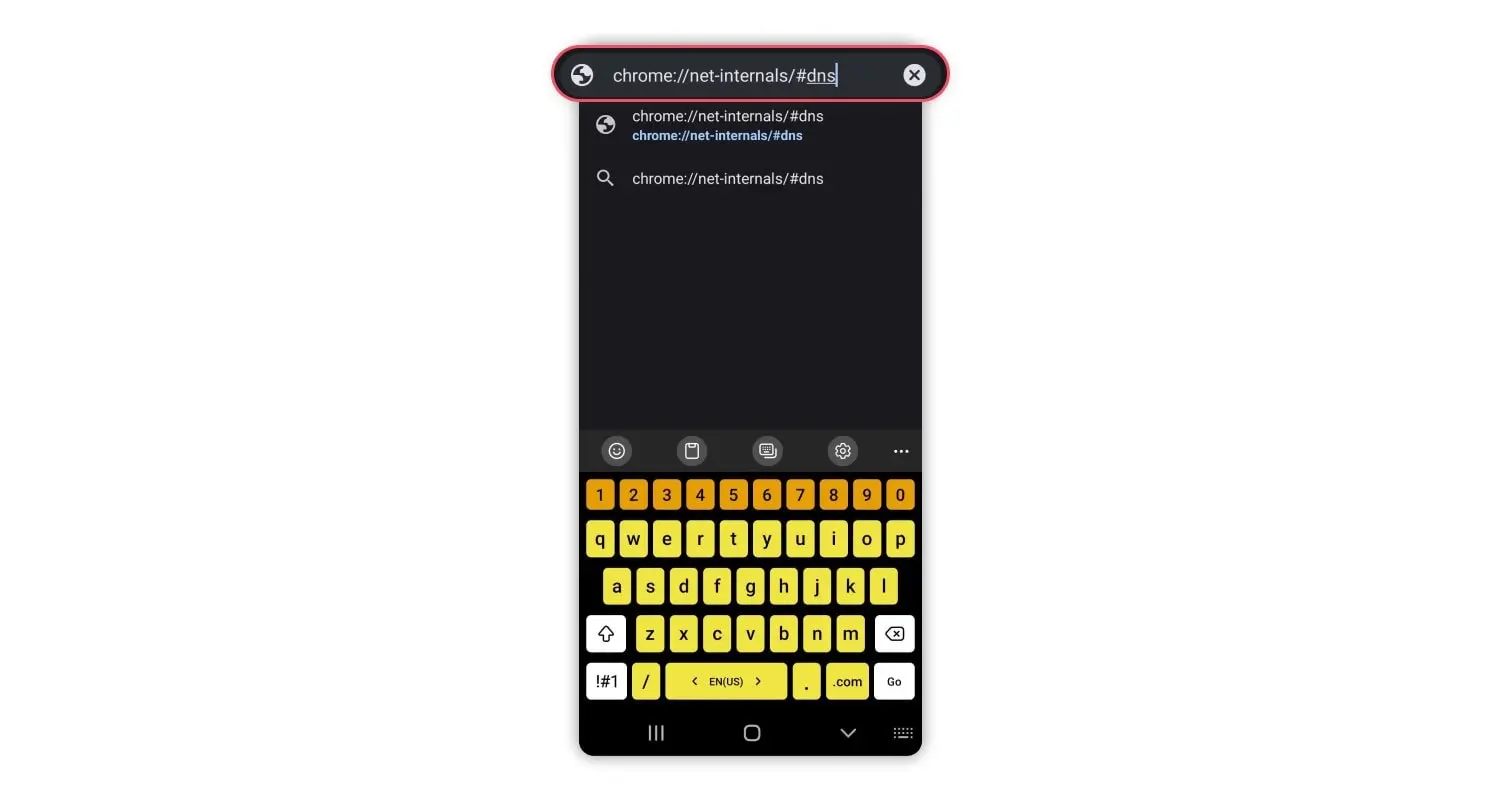
To delete incognito history on android, you need to:
- Open Google Chrome and type chrome://net-internals/#dns in the address bar.

- Click on “clear host cache” to delete DNS queries and remove incognito history.
iOS
If you need to delete incognito history on iphone or other iOS device, do this:
- If usingthe Google Chrome browser, follow the same steps for Android phones above.
- Alternatively, restart your iPhone or enable airplane mode for a few seconds to automatically flush all DNS records to clear incognito history

Now you know how to delete incognito history, but if you want to make sure nobody can see your browsing history, keep on reading: we’ll tell you how to make every browsing session genuinely secure!
How to browse privately
It takes a lot more than the glasses-and-hat disguise icon to cover your tracks and achieve greater privacy online. Stick to the following if you want to keep your private browsing history and sensitive data to yourself.

1. Choose a privacy-friendly browser
Web browsers like Chrome or Edge are the popular kids on the block. But they don’t care much about your privacy. You can be better off using more secure browsers — they block trackers and don’t log your data for profit.
2. Use a private search engine
Search engines, like DuckDuckGo, Mojeek, Brave Search, and others, let you browse the web without being tracked. They provide you with a completely unfiltered overview of the Internet and a safe way to search for things online.
3. Add browser extensions for extra privacy
If ditching Chrome seems like a stretch, you can go for browser extensions to get greater privacy. They can block scripts, ads, or trackers. Besides, they are easy to use with most browsers.
4. Secure your social media settings
Most social media companies earn revenue by collecting and selling user data to marketers and other third parties. But now that social media companies have given users greater control over their data, you can play with the settings to minimize data collection on these websites and apps.
5. Disable third-party cookies
Third-party cookies are tracked by websites other than the one you are visiting. Advertisers use them to track you across different platforms. While Google plans to phase out third-party cookies in Chrome by the end of 2024, you can already disable them manually through your browser.
6. Use a VPN connection
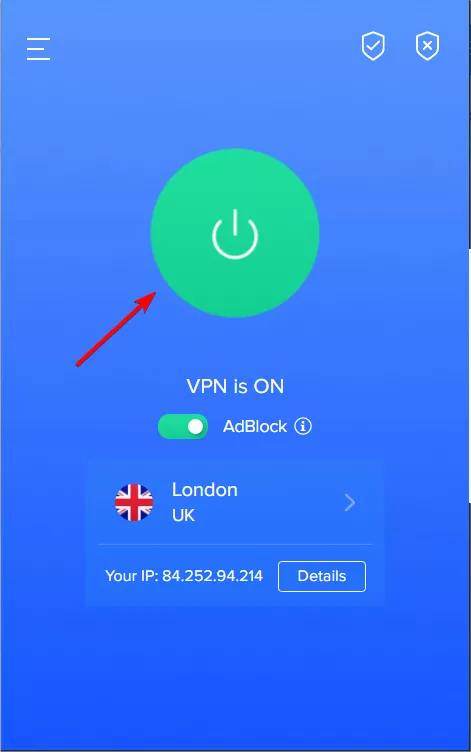
A VPN is a perfect remedy where incognito mode comes up short. By routing your traffic through an secure “tunnel” to a remote server and encrypting all your Internet traffic, VPNs secure all your data and mask your IP address. This prevents third parties from tracking you online. You just need to pick a reliable provider and let it help you privately browse the Internet without any worries.
How to dodge trackers with VeePN
You get a shot at Internet privacy with your data safe with next-gen AES-256 encryption and a new IP address from connecting to one of the 2,500+ VPN servers in 89 locations. VeePN goes even further with such advanced security features as NetGuard — it blocks ads, trackers, and malicious websites on the spot, adding privacy and security for your private browsing.
You can go about two ways here:
- Install a secure browser extension for Chrome, Edge, or Firefox and encrypt all your traffic for browsing privately.
- Get a dedicated VPN app for your PCand phone or both to protect all of the data coming in and out of your device — VeePN works on most popular operating systems.
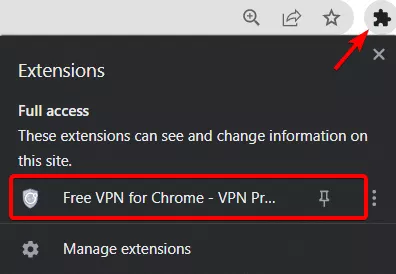
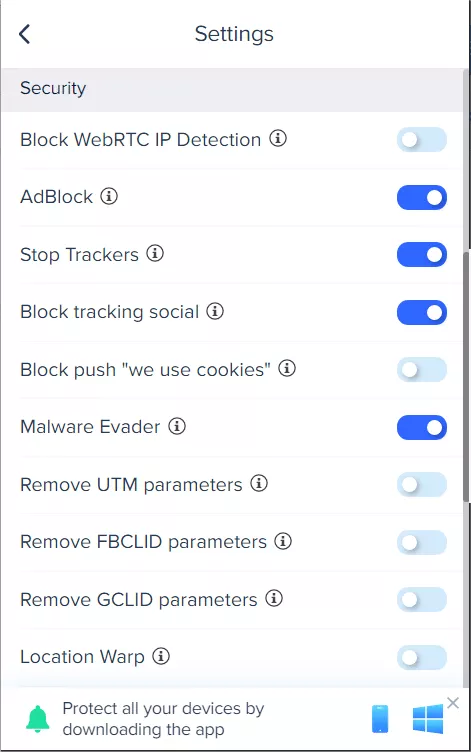
Picked a platform? Create a VeePN account and install the app or browser extension on your device and open it. Then, go to Settings to turn on tracking prevention. Here’s a step-by-step guide on how to do it on VeePN Chrome Extension:
- Go to Extensions by clicking on the puzzle icon and select VeePN.
- Go to the menu and click on Settings.
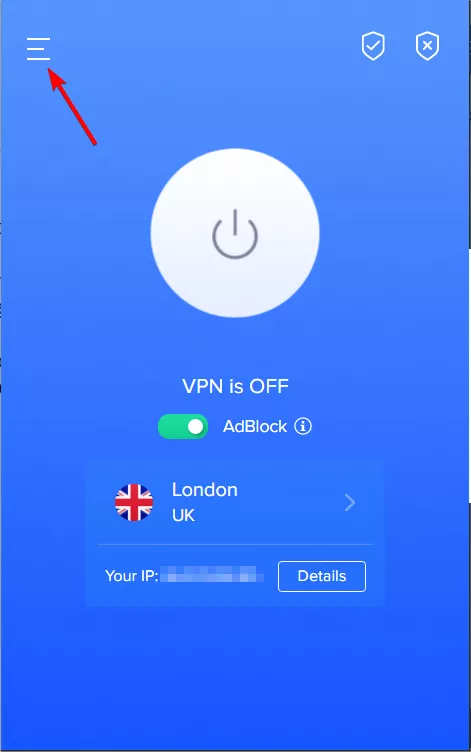
- Toggle on needed switches.
- Return to the main screen and click Connect.
And that’s it — enjoy the web with your tracks covered!
Bottom line
Let’s draw some conclusions.
- Incognito mode hides your browsing data from others who might look at/use your device — but not from the wider world.
- While your web activity isn’t saved on your device, the websites you visited, your ISP, your corporate network administrator, or search engines can still track your dns cache when you browse in incognito mode. We hope that this guide has taught you how to delete incognito history with little hassle involved.
- Add in using a VPN while going full incognito — this tandem will work well to let you enjoy truly private browsing.
So yeah, opening a new browser window in incognito mode doesn’t make you vanish under a cloak of invisibility with all your browsing history perfectly hidden from the world. Bummer.
FAQ
Yes, incognito mode doesn’t mean anonymous browsing. It hides your Internet activity from others who might look at/use your device. However, it doesn’t mask your IP address nor encrypt your data, which allows third parties to snoop on you. Learn more in this article.
Yep, incognito mode only clocks your Internet activity from others who might look at/use your device. Yet, the Wi-Fi router can still log that info and the network admin can always retrieve it later. Find out more in our blog post.
Incognito mode doesn’t save your browsing history on the device, but some data can still be accessed by network administrators, ISPs, or through router logs. To view incognito activity, you might check router history if you’re an admin, or use third-party tools that log network activity, though this is generally more complex.
To delete any traces of incognito browsing on an iPhone, clear your Safari or Chrome data directly:
- Safari: Go to Settings > Safari > Clear History and Website Data.
- Chrome: Open Chrome, go to Settings > Privacy > Clear Browsing Data, and select the data you want to delete.
This clears data like cookies or cache but won’t delete activity stored by network administrators or ISPs.
To delete traces of incognito browsing on an Android device:
- Chrome: Open Chrome, tap the three dots, go to History, then Clear Browsing Data. Select “Cookies, Site Data” and “Cached Images and Files” to clear traces of your session.
- Firefox: Tap the three dots, go to Settings > Delete browsing data, and select the data you want to delete.
This removes local browsing data but won’t clear any records saved by your network provider.
To delete traces of incognito browsing in Chrome:
- Open Chrome and go to the menu (three dots in the top-right corner).
- Select History > Clear browsing data.
- Choose the data types like Cookies and other site data and Cached images and files, then click Clear data.
This clears local data from the device but doesn’t affect any history logs stored by networks or ISPs.
To delete traces of incognito browsing on a Mac:
- Safari: Go to Safari > Clear History from the menu bar, then select the desired timeframe and click Clear History.
- Chrome: Click the three dots in the top-right corner, select History > Clear browsing data. Choose the data types you want to remove and click Clear data.
This will remove local data but won’t erase any records stored by your internet service provider or network.
VeePN is freedom