VDI vs VPN: Picking the Best Solution for Remote Teams
Remote work is here to stay, and how you secure access matters. If you are deciding between VDI and VPN, you are not alone. This guide explains VDI vs VPN in plain language, shows where each shines, and helps you choose the right fit for your team and budget.
Quick answer: a VPN creates an encrypted tunnel from an employee’s device to your private network. VDI hosts full desktops in a centralized environment and streams the session to the user. Both enable remote access, but they solve different problems.
TL;DR: VDI vs VPN recommendations
- Choose VPN if you need fast, cost-effective remote access to internal apps, have a small to midsize team, and can manage endpoint security on employee devices.
- Choose VDI if data must never leave your environment, you need strict access control and centralized management, or you support BYOD and contractors at scale.
- Performance tip: VPN depends on the user’s internet and device; VDI depends on low-latency network paths to the data center or cloud.
- Compliance tip: VDI simplifies governance by keeping sensitive data centralized. VPN requires stronger endpoint controls and policies.
Why secure networks when working remotely
Distributed teams face a few predictable risks:
- Unsecured public Wi-Fi. Some employees still use public hotspots, which are not safe. Companies should discourage this and secure network access regardless of where staff connect.
- Use of personal devices. At home, many rely on personal laptops and routers. Without managed antivirus, patches, and strong passwords, sensitive information is at risk.
- Heavy use of collaboration apps. Tools like Teams, Slack, and WhatsApp improve productivity but can also expand the attack surface. Pick safer apps and control access.
In short, organizations must protect connections and data wherever staff work. Two common choices are VPN and VDI. Let’s compare them.
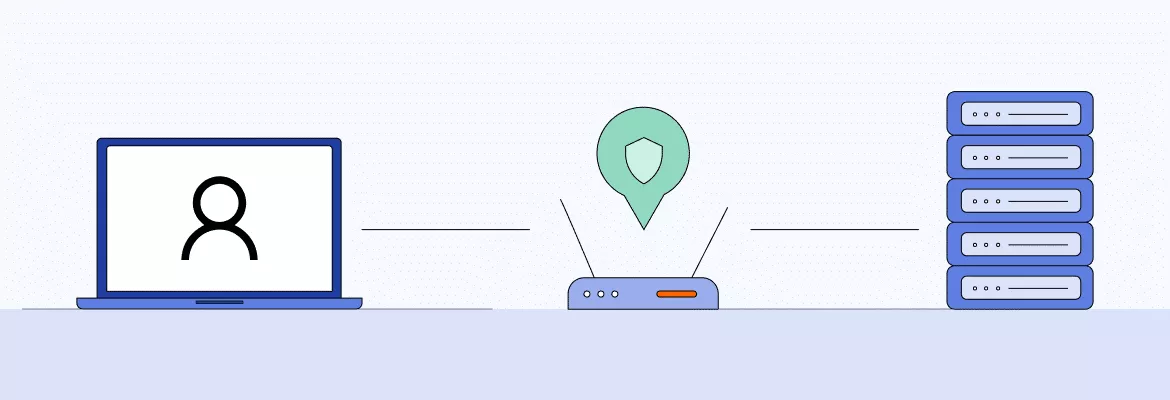
What is a Virtual Private Network (VPN)?
A VPN is an encrypted tunnel between an endpoint device and a private network. It is widely used to let employees connect securely to internal resources over the internet from laptops or PCs. In business settings, a VPN typically uses strong encryption and authentication so only authorized users gain access.
Beyond corporate use, VPNs are also popular for personal privacy and streaming. But in a work context, the focus is secure, authenticated access to company resources, typically with MFA, modern protocols, and clear access policies.
Authoritative guidance: NIST explains remote access and VPN security controls in its Telework, Remote Access, and BYOD Security guide and in the Guide to IPsec VPNs.
How a VPN works
A VPN client on the user’s device builds an encrypted tunnel to a VPN gateway on your network. All traffic to internal resources travels through this tunnel, protected from eavesdropping. Admins define access policies and typically require strong authentication, often with MFA. Because traffic reaches the endpoint, device hygiene matters: patching, EDR/antivirus, disk encryption, and sensible use of split tunneling reduce risk if data is saved locally. For certain tasks, some teams also compare VPN with remote desktop tools; see our take on how to secure these options.
VPN: pros and cons
VPN advantages
- Simple to roll out and use. Little on-premises infrastructure is needed, and employees can connect in a click.
- Cost-effective. Licensing and maintenance are straightforward compared to running virtual desktops.
- Flexible access. Works well for accessing file shares, intranet sites, and internal web apps.
- Mature clients and performance. Top-notch VPN clients and modern protocols can deliver solid speeds over diverse networks.
VPN drawbacks
- Endpoint risk. Data can be saved or copied to local devices unless policies and controls prevent it.
- Variable performance. Throughput and latency depend on the user’s internet and device resources.
- Operational discipline. Users must connect the VPN before accessing resources. Some teams explore a decentralized approach, but enterprise support and governance vary.
What is a Virtual Desktop Infrastructure (VDI)?
VDI hosts full desktop environments on centralized servers and streams the session to users over the network. Employees interact with a Windows or Linux desktop that actually runs in your data center or the cloud, not on their device. This keeps apps and data centralized and easier to control. Many organizations also consider Desktop as a Service (DaaS) offerings for similar outcomes.
For reference, see Microsoft’s Azure Virtual Desktop overview and VMware’s Horizon VDI documentation for how leading platforms approach VDI.
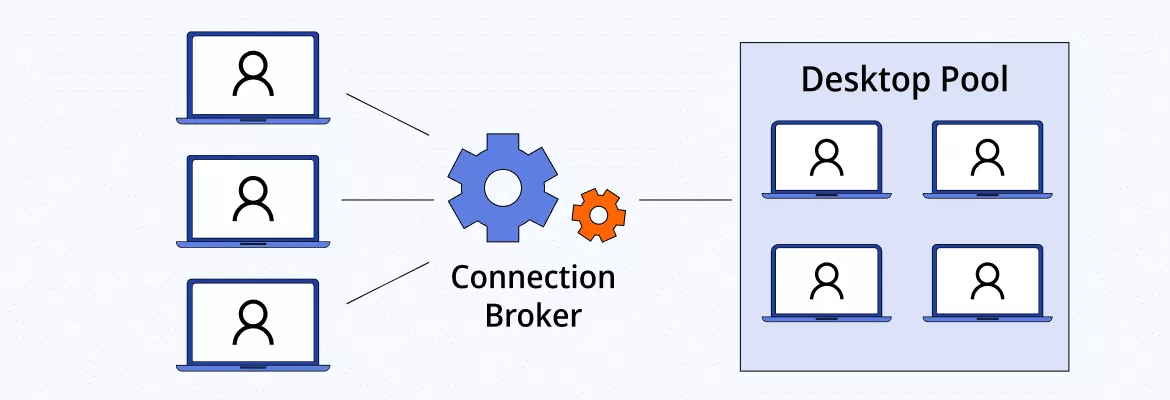
How VDI works
Core components typically include:
- Connection broker. Authenticates users and assigns them a desktop.
- Hypervisor. Virtualizes compute resources and runs desktop virtual machines.
- Desktop pools. Groups of desktops with a shared image and configuration.
A user logs in through a thin client or app, the connection broker assigns a virtual desktop, and the session is streamed to the endpoint. Processing happens on centralized servers or a dedicated server cluster. VDI can be deployed on-premises or in the cloud. User experience is sensitive to latency and bandwidth, so network quality is important. Microsoft’s guidance highlights latency thresholds and sizing for smooth Azure Virtual Desktop. In practice, success also depends on user profile management, storage performance, and whether workloads need GPU acceleration.
VDI: pros and cons
VDI advantages
- Centralized security. Apps and data stay in the data center or cloud. Access policies and DLP are enforced at the source.
- Consistent experience. Each user gets a managed desktop image with predictable performance.
- BYOD-friendly with guardrails. Personal devices become thin clients, while controls and logging remain centralized.
- Streamlined management. IT can patch, update, and troubleshoot from one place and push changes to all desktops.
VDI drawbacks
- Higher cost and complexity. Infrastructure, licensing, and scaling add up, and specialized skills are needed.
- Ongoing operations. Image management, capacity planning, and storage performance require dedicated effort.
- Training and change management. Users adapt to a new interface and workflows, and some peripherals or media workflows may need special handling.
VPN vs VDI: key differences
- Data location and security. VPN encrypts data in transit but allows it to reach the endpoint, which can store or copy files unless restricted. In VDI, sensitive data and apps remain on centralized servers. Admins can block clipboard, printing, and drive mapping to reduce data leakage.
- Applications. With VPN, users run apps locally or access via a browser. VDI installs apps on the virtual desktop image and streams them to users, which helps with license control and legacy software.
- Hardware and endpoints. VPN performance relies on the user’s device and home network. VDI offloads compute to servers, so endpoints can be lower spec, though graphics-heavy workloads may require GPU-backed VMs.
- Management and maintenance. VPN servers are simpler to maintain, but managing many disparate endpoints is harder. VDI centralizes updates and troubleshooting but adds image management and virtualization overhead.
- Cost and TCO. VPN is usually less expensive to adopt and run, especially for small teams. VDI involves infrastructure, storage, licensing, and operations that raise total cost of ownership.
- Performance and latency. VPN performance varies with the user’s internet link and device. VDI is sensitive to latency to the data center or cloud; well-placed regions and optimized protocols can deliver a near-native feel for most office tasks.
- Compliance and governance. VPN requires strong endpoint controls, MDM, and policies to keep regulated data off unmanaged devices. VDI simplifies governance because data stays centralized and access can be tightly audited. NIST emphasizes layered controls for remote access security.
VDI vs VPN: one-page comparison
| Dimension | VPN | VDI |
|---|---|---|
| Core model | Encrypted tunnel from endpoint to private network | Full desktop runs on centralized servers, session is streamed |
| Data location | Reaches the endpoint unless restricted | Stays in the data center or cloud |
| Applications | Run locally or access via a browser | Installed on the virtual desktop image |
| Endpoint dependence | High, device and OS matter | Low for compute; endpoints act as thin clients |
| Management | Simple core infra, complex endpoint fleet | Centralized updates, image and capacity management required |
| Performance | Varies with user device and ISP | Sensitive to latency to the VDI hosts |
| Cost/TCO | Lower startup and ongoing costs | Higher infra, licensing, and operations costs |
| Compliance | Requires strong endpoint controls | Simplifies data governance and DLP |
When to choose VPN vs VDI
Choose VPN when:
- Your team is small to midsize and cost-sensitive.
- Staff mainly need intranet sites, file shares, or a few internal web apps.
- Employees use company-managed devices with good endpoint security.
- Field work or travel leads to variable connectivity, and offline work is needed.
Choose VDI when:
- Regulated or confidential data must stay off endpoints.
- You support contractors or BYOD at scale and want consistent controls.
- You rely on legacy or license-limited apps that you do not want installed everywhere.
- You need centralized auditing, DLP, and tight access control across locations.
Mixed approach:
- Many organizations use VPN for general access and VDI for sensitive roles or apps. This balances cost with control and can phase in VDI where it delivers the most value.
Decision checklist
Use this quick checklist to pressure-test your choice:
- Where must sensitive data live? If regulated data can’t touch endpoints, lean VDI. If managed devices and endpoint controls are acceptable, VPN can work well.
- Who owns the devices? Large BYOD or contractor populations push you toward VDI; a primarily corporate-managed fleet favors VPN.
- What apps do you run? Legacy, license-limited, or tightly controlled apps are easier to centralize with VDI; lightweight web apps and file shares are fine over VPN.
- How good is user connectivity? Highly variable or offline work suggests VPN with local apps; consistent low-latency links to a region near users make VDI shine.
- What’s your team capacity? If you lack skills or time for image, capacity, and storage management, VPN is simpler; if you can invest in centralized ops, VDI pays off.
- What’s your budget and timeline? Need something fast and affordable? Start with VPN. Planning a strategic refresh with stronger governance? Scope VDI or DaaS.
- How fast do you scale up/down? Seasonal or contractor swings are smoother with VDI or DaaS pooling; stable headcount can keep VPN costs minimal.
- Do you need airtight audit trails and DLP? VDI simplifies centralized logging and policy enforcement; VPN requires stronger endpoint and data controls.
Rule of thumb: Start with VPN for general productivity, then introduce VDI for high-risk roles, regulated datasets, or specialized apps.
A quick note on printing, media, and peripherals
Peripherals can make or break remote experience. With VPN, users typically print through native drivers to local printers and use webcams, headsets, and storage as usual. This is simple but increases data egress risk if documents or files are stored locally. With VDI, USB redirection, webcam and audio optimization, and printer mapping depend on platform features and policies.
Many teams allow only virtual printing or session printers while blocking clipboard, drive mapping, and mass-storage redirection to keep data centralized. Media-heavy workflows like video conferencing or 3D apps may need protocol optimizations and GPU-backed VMs to feel natural. Always test your top peripherals and collaboration tools in a pilot before broad rollout.
Conclusion
Both VPN and VDI enable productive remote work, but they solve different problems. VPN wins on speed to deploy, cost, and simplicity when you trust your endpoints and mostly use web apps, file shares, and intranet tools. VDI wins on centralized security, governance, and consistent experiences across diverse or unmanaged devices, especially for sensitive data and legacy applications.
In practice, the best answer is often hybrid: use VPN for everyday tasks and VDI for your most regulated teams and apps. Align the choice with your data sensitivity, device mix, app portfolio, network realities, and operational capacity—then pilot, measure user experience, and iterate.
FAQ
VDI generally offers stronger data control because applications and files stay in the data center or cloud instead of landing on endpoints. That said, a well-managed VPN with hardened, monitored devices can be very secure. The difference is where security work concentrates: VDI centralizes it, while VPN distributes it across every endpoint.
Yes. Many organizations deliver VDI to sensitive users and apps while keeping VPN for general access. Some even front VDI with VPN for an extra layer or to reach internal brokers, though modern deployments often publish VDI securely without requiring a separate tunnel.
Not necessarily. Modern VDI and DaaS platforms can be published securely over the internet with strong authentication and gateway services. A VPN may still be used for certain network paths or policies, but it is not a requirement for most contemporary setups.
Small teams often start with VPN because it is quick to deploy and affordable. If the business handles highly sensitive data or relies on tightly controlled legacy apps, a targeted VDI or DaaS deployment for specific roles can make sense even at small scale.
VPN typically has lower upfront and ongoing costs, mainly covering gateway capacity, licensing, and endpoint management. VDI involves infrastructure or service consumption, storage performance, licensing for virtualization and desktops, and ongoing image and capacity management, which increases total cost of ownership.
Graphics-intensive apps and high-quality video conferencing generally perform better when compute is close to the user. Over VPN, workloads run locally on the endpoint. Over VDI, you may need GPU-enabled virtual machines and protocol optimizations to achieve a smooth experience, and latency to the VDI region is critical.
Zero Trust Network Access can replace or augment VPN for app-level secure access, reducing broad network exposure. It does not replace VDI, which delivers full desktops and centralizes data. Many organizations pair ZTNA with either VPN or VDI to tighten access controls while matching the right delivery model to each use case.
VeePN is freedom
Download VeePN Client for All Platforms
Enjoy a smooth VPN experience anywhere, anytime. No matter the device you have — phone or laptop, tablet or router — VeePN’s next-gen data protection and ultra-fast speeds will cover all of them.
Download for PC Download for Mac IOS and Android App
IOS and Android App
Want secure browsing while reading this?
See the difference for yourself - Try VeePN PRO for 3-days for $1, no risk, no pressure.
Start My $1 TrialThen VeePN PRO 1-year plan








